These days, organizations face several challenges. For an IT administrator, it’s probably limiting access to unauthorized devices like external hard drives, printers, and other peripherals that serve as a major problem.
Good thing that Microsoft is aware of this challenge. That is probably the reason they rolled out the layered Group Policy feature to allow network administrators to decide what can be installed on devices on the organization’s network.
The Group Policy Editor has always been one of the most powerful tools on Windows for IT administrators. With each version, Microsoft has added new ways to create and manage Group Policy objects (GPOs).
One thing that hasn’t changed is the need to understand how Group Policy works before you can successfully implement it within your enterprise. This guide provides an introduction to managing Group Policy and how to use a layered Group Policy on Windows 11.
Group Policy on Windows Devices: A Quick Overview
Before anything else, what is Group Policy?
It is a Windows feature where network administrators can manage and control a vast range of settings. It serves as a centralized place for system admins to configure applications, user settings, and others.
When used properly, the Group Policy Editor allows organizations to improve the security of the computers and other devices within the same network. It will help defend the network against threats, malware, and other attacks.
What Is a Group Policy Object (GPO)?
GPOs are a group of settings that are created using the Microsoft Management Console Group Policy Editor. These objects can be associated with various Active Directory containers, such as domains and sites.
Group Policy Objects can be used in many ways for security purposes. Below are some example scenarios:
- A GPO can be used to set a landing page that a user sees when launching their browser or opening a new tab.
- System administrators can use a GPO to define what network-connected printers will appear on the list of available printers in the network.
- A GPO can also be used to change some security practices and protocols, such as setting internet connection restrictions and screen time.
How Are GPOs Processed?
The hierarchy of which GPOs to be processed will affect the settings applied to the user’s device. This hierarchy is called LSDOU, which is an abbreviation for local, site, domain, organizational unit.
With LSDOU, the local computer policy is processed first. It will be followed by site level to domain ad policies. Finally, the organizational units are processed. If a policy conflicts with LSDOU, then the last applied policy wins.
Why Use Group Policies?
So, should you use these policies? Will you benefit from them?
Of course, you can. Group Policies can ensure that your sensitive data is safe against hackers and that your IT infrastructure is set up the right way.
It’s surprising to know that Windows is not as secure as you thought it would be. Thankfully, GPOs are designed to address any security gaps within the operating system. For instance, they allow you to implement a policy where users have limited access to tools required to do their job.
However, the benefits of the Group Policy Editor are not limited to security alone. Below are other advantages of implementing group policies:
- Systems Management – A group policy can be used for simplifying tasks that are time-consuming. Apply this to save hours of time trying to configure the environment of a new user joining your organization.
- Password Policy – A lot of organizations are operating with a no-password policy, and others even allow users to set credentials that don’t expire. As we all know, passwords that are not regularly changed are at risk of being hacked. With a group policy in place, organizations can set rules in creating passwords, including parameters like length and complexity.
- Health Checking – You can use a group policy to deploy app and software updates. Doing this will ensure that your environment is healthy and protected against security threats.
What Is the Layered Group Policy Feature on Windows 11?
The layered Group Policy feature is a new functionality introduced by Microsoft on Windows 10/11 and Windows 11 devices. Here’s how the software giant describes the feature:
“Device installation policies are used to restrict the installation of any device, both internal and external, to all machines across an organization while allowing a small set of pre-authorized devices to be used/installed. Every device has a set of ‘device identifiers’ that are understood by the system (class, device ID and instance ID). The allow list, which is written by the system admin, contains sets of identifiers that represent different devices – this way a system understands which device is allowed and which is blocked.”
The goal of this feature is to protect machines against corruption, reduce the number of support cases within organizations, and most importantly, avoid data theft. This policy can be applied to restrict the installation or use of devices in an internal or external organization. Basically, IT administrators have full control over what devices can be installed or used.
Does a Layered Group Policy Work on Windows 10/11?
For WinAero users, a layered Group Policy may not be new as it was first rolled out in the Windows 10 version 21H2. As for other Windows 10 versions, this policy has been rolled out by Microsoft only last July 2021.
The restriction policies can be set using certain device identifiers, which Windows 10/11 is already familiar with. These identifiers include class, instance IDs, and device IDs.
This feature’s allow list needs to be written by the system administrator, and it contains a set of identifiers that each represents a specific device. Through this list, the system can determine which devices can be granted access and which ones should be blocked.
With this Layered Group Policy added, system administrators can benefit from:
- Intuitive Usage – With this policy, system administrators don’t have to know the device classes to prevent the installation of other USB classes. It allows them to just focus on scripts.
- Flexibility – Aside from intuitive usage, this policy introduces hierarchical layering in this order: Instance ID, Hardware IDs, and compatible IDs, Class, and Removable Device Property.
How to Apply a Layered Group Policy on Windows 11
A Layered Group Policy can be conveniently accessed and applied by following this path:
Computer Configuration -> Administrative Templates -> System -> Device Installation -> Device Installation Restrictions.
Once in the Device Installation Restrictions folder, the first policy that needs to be enabled is the Apply layered order of evaluation for Allow and Prevent device installation policies across all device match criteria. After this, there will be another set of policies that need to be enabled in a hierarchical order: Device Instance IDs -> Device IDs -> Device Setup Class -> Removable Devices.
Here’s a better explanation for each one of these:
- Device Instance IDs – It is a unique, system-supplied device identification string that can identify new devices in a system. The Device Instance IDs prevent the installation of other devices, which use drivers that match them. Likewise, these IDs allow the installation of devices that use drivers that match them.
- Device IDs – Windows uses this string to match a device to a driver package. This string can range from very specific to generic ones. Device ID strings can either be hardware IDs or compatible IDs. The Device IDs prevent the installation of devices, which use drivers that match them. These IDs can also allow the installation of devices, which use drivers that match them.
- Device Setup Class – Also called Class, this is another type of identification string. It is the manufacturer of the device that assigns the class to a device in the driver package. The device setup class prevents the installation of devices, which use drivers that match them. It also allows the installation of devices, which use drivers that match them.
- Removable Devices – These parameters are used to prevent the installation of removable devices. Removable Devices can be configured by adding the class ID or the device ID. Then, apply the changes.
Because of the policy’s layered structure, it can be used over the Prevent installation of devices not described by other policy settings feature.
How to Find Compatible IDs and Hardware IDs
To find compatible IDs and hardware IDs, follow these steps:
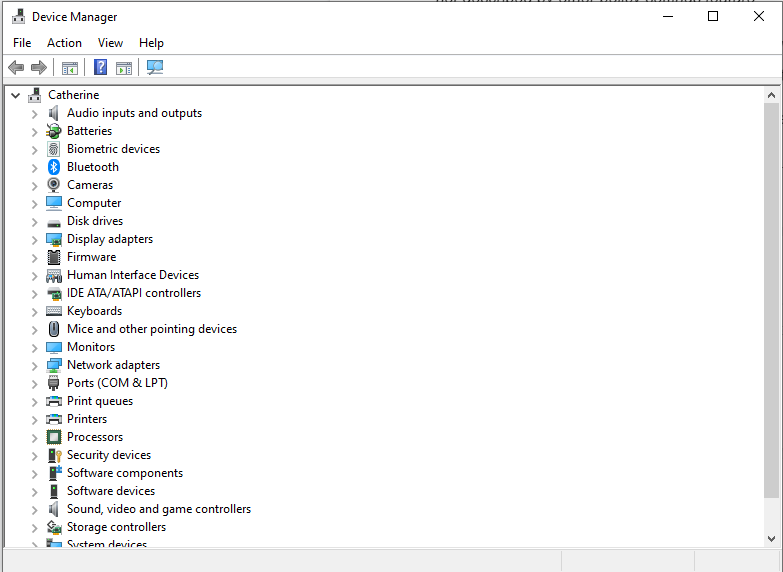
- Access the Device Manager using the Windows + X Select Device Manager from the list.
- Right-click the device.
- Select Properties.
- Access the Details
- Click Property to find the details you need, such as hardware ID, class ID, and others.
How to Add a Device ID to the Allow List
To add a device ID to the Allow list, simply refer to the steps below:
- Open the Allow installation of devices that match any of these device IDs
- Choose Enabled.
- Go to the Options section and click the Show
- Add a Hardware ID or a Compatible ID to the list.
- Save the changes by hitting the Apply
How to Allow System Administrators to Override Device Installation Restrictions
You need to enable a certain policy to allow overriding of device installation restrictions. Once it is enabled, system administrators can use the Add Hardware or Update Driver wizard to install and update the device.
Summary
In this article, we’ve shown you how to implement a layered group policy for your Windows 10/11 environment. We’ve also discussed what a group policy is and how it will benefit your organization. We hope this has been helpful! If there is anything else we can do for you, please let us know by reading more or visiting our website today.
