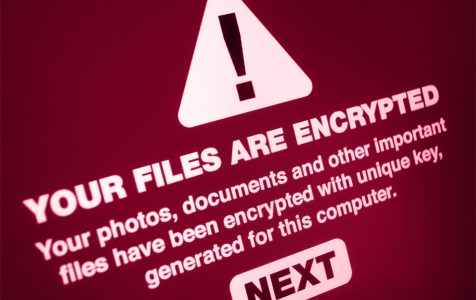
The most troublesome and dangerous malware ever invented by man is probably the ransomware. The effects are so abrupt and users usually don’t have a chance to prepare before being targeted by this malware. There are no symptoms, no danger signs, and no clues whatsoever. You’ll just log into the computer one day and find that all your files have been encrypted and that you can no longer access them.
The insidious part of this attack is that you have to pay a ransom fee to the attackers for them to release the decryption key that would give you back access to your files. They usually demand payment in the form of bitcoin or other cryptocurrencies. Unfortunately, paying the ransom does not guarantee that the cybercriminals will keep their word and send you the correct deception key. In most cases, the attackers no longer reply after getting the money. And if they do give the decryption key, there is a high chance that some of your files won’t be decrypted properly and get lost forever.
Though some ransomware variants can be decrypted using free decryption tools developed by security experts, newer and more sophisticated ransomware can be difficult to deal with. Zipe ransomware belongs to this highly dangerous type of malware. When you get infected by Zipe ransomware, getting back your files is almost impossible, unless you pay the ransom fee. It is one of the most dangerous types of ransomware used by attackers these days.
This article aims to provide users the latest information about the Zipe ransomware, what it does, how to avoid it, and what you need to do in case your computer gets affected.
What is the Zipe Ransomware?
Zipe ransomware is an encryption-based malware that is associated with the Djvu family. Zipe ransomware was first exposed publicly on June 2020 by security experts who were able dissect the core components of the virus and trace it back to the Djvu ransomware family. By analyzing its core components, ransom note, payload, and encryption model, it has become clear that this crypto-malware was evolved from this old ransomware family. The Djvu ransomware family is known for using RSA Salsa20 encryption algorithm to encrypt the user’s personal files.
When this ransomware’s payload is downloaded to the victim’s computer, it works in the background in phases – from the infiltration to the launch of the cipher to manifestation. And just like the previous Djvu variants, Zipe targets more than 200 file types to encrypt, which all end up getting the .zipe file extension. The ransomware may skip some personal or other files that it is not compatible with, but some of the common file extensions that Zipe ransomware targets include 7z, .aif, .arj, .ai, .bmp, asp, .bin, .cda, .csv, .css, .mid, .midi, .dat, .dbf, .docs, .docx, .deb, .dmg, .log, .iso, .ico, .jpeg, .jpg, .mp3, .mpa, .ogg, .wav, .wma, .wpl, .pkg, .rar, .rpm, .toast, .vcd, .sav, .tar, .xml, .gif, .png, .svg, .part, .rss, .xhtml, .zip, and others.
The Zipe crypto-ransomware is extremely dangerous because it may cause permanent loss of your important files. What makes it more difficult to handle is that the encryption technology that it uses to lock your files cannot be brute-forced. This means that that it cannot be decrypted using the regular Emsisoft’s STOP/Djvu decryption tools. The only way to recover the encrypted files is to pay the ransom to the criminals, which is between $490 to $980 in Bitcoins depending on how fast the victim responds.
Once the files have been encrypted, they are assigned the .zipe file extension and the thumbnails are switched to a simple white image without any logos. The user is not able to open, rename, move, or copy any of the locked files. The user can’t do anything with the files unless he or she pays the ransom.
Just like most Djvu variants, such as Sqpc, Mzlq, or Koti, the Zipe ransomware drops a note in every folder that contains locked files, urging the victim to pay a certain amount in Bitcoins within 72 hours. If the victim fails to pay within the deadline, the price will double to $980, and it will continue to increase until the victim decides to give in. The _readme.txt ransom note can also be found on the desktop so the user can easily notice it. Aside from the ransom fee, the attackers also leave a pair of email addresses where the victim can contact the attackers: “helpmanager@mail.ch” and “restoreadmin@firemail.cc”. The attackers may also offer to decrypt one locked file for free to prove that they are able to unlock the files.
This is the ransom note that cybercriminals who distribute ZIPE ransomware leave on the victims’ computers:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-gSEEREZ5tS
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
helpmanager@mail.ch
Reserve e-mail address to contact us:
restoremanager@firemail.cc
Your personal ID
How Did Zipe Ransomware Get Into Your System?
The Zipe ransomware is usually distributed using spam emails with infected attachments or by exploiting vulnerabilities in your operating system and other installed software.
Here are some of the ways that Zipe ransomware can infect your computer:
Attackers often spam out a legitimate-looking email from a legitimate organization, complete with forged header information. This aims to trick you into believing that it is from an authentic shipping company, such as DHL or FedEx. The email informs you that the courier tried to deliver a package to you, but the delivery failed for some reason. You might also get an email claiming to be notifications of a package you have sent. Whatever the content of the email is, the bottom line is that it is designed to tempt you to download the attached file or click on a link inside the email. These actions will download Zipe ransomware on your computer.
The Zipe ransomware can also attack victims by exploiting vulnerabilities in the applications or software installed on the computer. Commonly exploited programs include the operating system itself, Microsoft Office, browsers, and other third-party applications.
Aside from these methods, Zipe ransomware can also be downloaded as an additional payload by other malware.
What Should Victims of Zipe Ransomware Do?
If your computer ever gets infected by the Zipe ransomware, do not pay the ransom just to get your files back. Paying the ransom fee does not guarantee that the attackers will release your file. Instead, you should remove Zipe ransomware from your computer as soon as possible. But before that, copy and paste all the encrypted files into an external drive to prevent permanent data loss.
Once you have created a copy of the encrypted files and removed the malicious ransomware from your computer, you can then try to recover the files, which we will explain in the next section.
You can also report the attack to your government’s agency assigned to monitor fraud and scam sites. Here are some of the links you can try:
If your computer is infected with this ransomware, we recommend that you contact the following government fraud and scam sites to report this attack:
- United States – Report the attack on the On Guard Online
- Australia, – Report the attack on the SCAMwatch
- Canada – Report the attack on the Canadian Anti-Fraud Centre
- France – Report the attack on the Agence nationale de la sécurité des systèmes d’information
- Germany – Report the attack on the Bundesamt für Sicherheit in der Informationstechnik
- Ireland – Report the attack on the An Garda Síochána
- New Zealand – Report the attack on the Consumer Affairs Scams
- the United Kingdom – Report the attack on the Action Fraud
For countries not included in this list, you can contact your local police or cyber crime agency to ask where you can report this kind of attack.
Zipe Ransomware Removal Instructions
Keep in mind that removing the Zipe ransomware from your computer can lead to your files being permanently lost, so you need to make sure you have a backup ready just in case. Even if you are not able to decrypt them now, someone somewhere could come up with a decryption tool that is able to unlock your files in the near future. Plus, you can also try some methods to try and restore your file.
To completely remove the Zipe ransomware from your computer, follow the steps below:
Step 1: Boot Into Safe Mode with Networking.
Getting rid of the Zipe ransomware can be troublesome since you won’t be able to disable it while all of its processes are running. To do this, you need to boot into Safe Mode with Networking and delete the ransomware through this mode. To boot into Safe Mode with Networking on Windows 10/11, do the following:
- Click on the Windows logo, then click the Power icon.
- Choose Restart while continuously holding the Shift button on the keyboard.
- In the Choose an option window, select Troubleshoot > Advanced Options.
- Click Startup Settings, then choose Restart
- Click on the F5 button to select Enable Safe Mode with Networking.
Your computer will restart and the Safe Mode environment will be launched.
Step 2: Run Your Antivirus App.
While in Safe Mode, the next thing you have to do is to scan your computer for the ransomware application and files. You need to choose a reliable anti-malware program to make sure that all components of the Zipe malware are detected and removed completely from your computer. You might need to restart your computer once the ransomware has been purged.
Step 3: Use System Restore.
If for some reason, you cannot boot into the Safe Mode with Networking environment, you can try doing a system restore to bring your system back to a time before the ransomware attack. Take note that this will only apply if you have created a previous system restore point prior to being infected by the Zipe ransomware.
To do a system restore, follow the instructions below:
- Restart your computer, then continuously press the F8 button when restarting.
- When the Advanced Option appears, choose Safe Mode with Command Prompt, then press Enter.
- In the command prompt window, type in cd restore, then press Enter.
- Next, type in rstrui.exe, then press Enter.
- Click Next.
- Choose a restore point from the list, then click on Next. Make sure to choose a restore point before the Zipe malware infected your device.
- Click Yes to confirm your choice.
The system restore process might take a few hours, depending on how many files you have on your computer. Make sure that the process is not interrupted to prevent errors.
Step 4: Restore Encrypted Files.
If the system restore did not work for some reason, you can try restoring your files manually. There are two ways you can do this: restoring the file to its previous version or by using a data recovery program.
To restore encrypted files to their previous version, you need to follow these steps:
- Right-click on the file then choose Properties.
- Choose the Previous Version tab.
- Select a Restore Point, then click the Restore button.
Follow the same steps for all of the encrypted files. This process could take some time, depending on how many files were affected by the Zipe ransomware. For faster data recovery, you can try third-party tools, such as EaseUS Data Recovery Wizard, MiniTool Power Data Recovery, Disk Drill, Data Rescue, Recuva, and Wondershare.
How to Avoid Zipe Ransomware Infection
Getting your computer infected by the Zipe ransomware can be quite a headache, especially right now that there is no available decryption tool that can unlock the encrypted files. So to prevent Zipe ransomware, and all other types of malware for that matter, from infiltrating your system, you need to tighten your computer’s security. Here are some of the things you can do to keep these threats at bay:
- Update your operating system at all times, including your applications. This will prevent malware from attacking any of your system’s vulnerabilities.
- Install a good antivirus program and schedule a sweep of your system regularly.
- Do not open email attachments from unknown or suspicious senders. The same rule should apply to links found on the email’s body.
- Check the authenticity of the sender. Verify if the sender actually sent you an email.
- Do not visit random websites.
- Use a VPN to protect your identity and your personal data.
They say prevention is better than cure, and no other proverb describes best the case of Zipe ransomware.