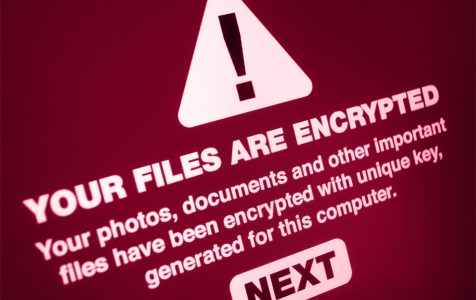
Almost every year, there is news of a new ransomware strain that seeks to take advantage of security flaws in popular operating systems, and to exploit user mishaps such as clicking attachments on infected emails. So common are the ransomware attacks that in 2019 alone, a ransomware attack took place every 14 seconds. The total payouts that year amounted to a staggering $11.5 billion, which is more money than the GDP of some nations.
So, how did we get here and what can we do? It is always best to begin with some knowledge of some of the malware entities that you are likely to encounter. Here is a list of the 10 most dangerous ransomware:
1. WannaCry
The WannaCry ransomware is perhaps the world’s most famous ransomware threat. It started infecting computers in 2017, and by the time it was done, hundreds of thousands of devices around the world had their files encrypted.
In the same year that the virus become active, it was formally asserted by the US, Australian, and British intelligence services that North Korea was behind what remains the successful ransomware attack in history. The total loss to businesses, individuals, and governments is estimated to be billions of dollars. To infiltrate computers, the malware creators relied on a Windows exploit called EternalBlue, which had earlier been discovered by the NSA. It is believed that the exploit was likely stolen from the NSA by the Shadow Brokers hacking group.
2. Bad Rabbit
The Bad Rabbit ransomware attack followed soon after WannaCry had been dealt with. It too mainly targeted Eastern European nations, such as Russia, Ukraine, and Turkey. There were also reports of attacks in Germany and other Western European nations.
This data encrypting malware was spread through a malicious Adobe Flash Player download which was injected in some popular software download websites. Once the victim downloaded the infected and obviously fake Adobe Flash Player, the Bad Rabbit ransomware would then start encrypting all the files and folders on the victim’s computer.
It would then lead the victims to a site where a ransom request of $280 in bitcoins would be placed for the option of decrypting the files.
3. Locky
The Locky ransomware is one of the most successful ransomware families out there. It cost businesses, individuals, and governments an estimated $1 billion in ransomware payments in 2016 alone. And despite being idle for some time, cybersecurity researchers point out that it has now morphed into ‘Diablo’ and ‘Lukitus’ variants, which are currently wreaking havoc on the PC universe.
Locky is usually spread through phishing campaigns that are aided by the Necurs botnet. As many as 35,000 emails distributing the Locky malware are being sent to victims. They use click-bait tactics such as offering ridiculous discounts on some luxury items to lure their victims into clicking links and infected attachments.
Once the malware enters the computer system, it is game over as it will quickly move to encrypt all files and folders, after which it will leave a readme.txt detailing the ransom to be paid and how the payment is to be made. Failure to pay the ransom amount means that your files will be permanently deleted.
4. Jaff
Jaff is a ransomware program that also relies on the Necurs botnet to send malicious emails to its victims. It can send up to 5 million emails in an hour, which is enough to overwhelm even the most careful computer user. Compared to other ransomware variants, Jaff is a bit more ambitious as it requests a ransom payment of up to $3000, while the typical ransom payout is usually several hundred bucks.
5. SamSam
SamSam is a ransomware that has been active in the US since 2016. The cybercriminals behind it exploit vulnerabilities in Windows servers to gain persistent access to a victim’s network and to infect all reachable hosts. Because the malware enters the victim’s computer through an approved access point (stolen credentials), detecting an intrusion is often difficult. As it spreads, SamSam likes to keep a low profile. It also gathers as much data about the victim as possible to make certain that the target is a worthy ransomware target.
After it is done with its infiltration, the malware will encrypt all files and folders and display a message detailing the terms of decryption. The ransom can be anywhere from several thousand dollars to hundreds of thousands depending on the target.
6. CryptoLocker
CryptoLocker is a potent ransomware entity that made a killing between 2013 and 2014. So effective was this strain of ransomware that it took an international effort, involving several governments to bring it down. But not before it made millions of dollars in ransom payments to its creators.
CrytoLocker was able to spread using the Gameover Zeus Botnet a back door Trojan that gives cyber-criminals the ability to control a network of computers. Once inside your computer, the CryptoLocker will encrypt your files using asymmetric encryption, and then display a ransom note indicating the ransom fee and the payment conditions.
7. PureLocker
The PureLocker ransomware, which attacks both Windows and Linux based systems, was active in 2019. The reason that makes the PureLocker ransomware entity dangerous is that it uses PureBasic, a programming language that is not all that popular, which means that many anti-malware solutions have a difficult time detecting signatures from the PureBasic binaries.
Although the ransomware uses many novel techniques to infect devices, a lot of its code is copied from known ransomware families such as the “more-eggs” ransomware family. It is believed that the underworld criminal groups Cobalt Group and the FIN6 gang are behind the ransomware.
8. TeslaCrypt
TeslaCrypt appeared in 2016 and was initially thought to be a variant of CryptoLocker, but it was soon discovered that it had a different modus operandi. The ransomware targeted ancillary files that are associated with video games, such as maps, saved games, and other downloadable content. Gamers save such files locally rather than on the cloud for quick access and for their importance to the gaming process.
After encrypting these files, TeslaCrypt requested $500 in bitcoins as ransom payment. Later during the same year and for unknown reasons, the malware creators decided to end their malicious activities and subsequently released a free tool that could decrypt the infected computers.
9. Cerber
Cerber is ransomware that is distributed as a Ransomware-as-a-Service (RaaS) on the dark web. Anyone can buy the malware and use it to infect their organization of choice for a 40% commission.
It uses a phishing campaign that involves sending thousands of infected Microsoft Word documents via email. Once downloaded or clicked the MS Word documents instigates an infection process that encrypts all the files and folders.
Cerber peaked in 2017 where it accounted for 26% of all ransomware attacks.
10. Ryuk
The Ryuk ransomware entity is a ransomware that gained notoriety in 2018 and 2019. It mainly targeted high value organizations such as healthcare providers and municipal governments in the US.
The ransomware uses advanced encrypting algorithms to lock users out of their files and to subsequently leave a note detailing the ransom terms and conditions. One of the novelties of the ransomware is that it can disable the Windows System Restore option on infected computers. This act makes it a lot harder to recover data that has been encrypted. Cybersecurity researchers believe that North Korea is behind the Ryuk ransomware.
How to Prevent Ransomware Attacks
How do you prevent any of the named ransomware variants from infecting your computer? We highly recommend that you begin by installing a powerful anti-malware solution as Outbyte Antivirus because as you have probably deduced, most ransomware attacks are aided by botnets which are easy to detect and stop if you have a reliable anti-malware solution.
To infect your computer, ransomware rely on various vulnerabilities in the Windows OS and installed apps. That’s why you need to keep your computer up-to-date at all times. For this, you can use a variety of tools, including a driver updater.
Lastly, but perhaps most importantly, have a backup of your files at all times so that in the unlikely scenario that you become end up as a victim of a ransomware attack, you will still have your files with you.