A ransomware is a malicious program that holds a computer’s files and folders for ransom. It does this by encrypting the files and folders in a manner that renders them inaccessible to anyone without the decrypting keys.
In recent years, starting 2012, there has been a notable increase in new strains of ransomware. An example is the TeslaCrypt ransomware Trojan.
The TeslaCrypt ransomware was first discovered in 2015, and it belongs to the CryptoLocker family of ransomware, or at least it shares significant similarities with the CryptoLocker strain as seen from its modus operandi and form. The two malware entities do not share any code, however. TeslaCrypt is able to infect computers through multiple exploit kits, such as Angler EK, Nuclear EK and Sweet Orange.
What Can TeslaCrypt Ransomware Do?
In its early years, the ransomware targeted game-play data for specific PC games. Once it infects a computer, it would search for 185 file extensions related to 40 different games. Some of the games include World of Warcraft, Minecraft, the Call of Duty series, and the World of Tanks. The data targeted include players profiles, saved games, custom maps, and game mods. Making such data unavailable to the players is enough to make the games unplayable. Worse, it takes years for players to build a reputable profile. If they do not agree to the ransom terms, their profiles may be lost forever. Newer variants of the ransomware have since extended the file types that are targeted for encryption.
TeslaCrypt demands a ransom of $500 worth of bitcoins in order to decrypt a victim’s files and folders.
How to Remove the TeslaCrypt Ransomware
After its release in 2015, the creators of the ransomware claimed that it used asymmetric encryption, but cybersecurity researchers soon discovered that the claim was not true. This made it possible for the researchers to create a decrypting tool that took advantage of this deficiency.
In its second iteration, which is the TeslaCrypt 2.0, the malware creators were able to rectify their mistake, but the malware still had deficiencies that were again easily identified.
Why does this information matter? Because TeslaCrypt has since become defunct and that the only thing you need to remove it from your computer is a powerful anti-malware solution such as Outbyte Anti-Malware.
Part of the reason that it has become defunct is that the exploits that allowed it to infect Windows devices no longer exist as Microsoft and the affected software companies have since patched the vulnerable software.
So, while it is unlikely that TeslaCrypt will ever infect your computer, removing it is easy. All you need to do is to run your Windows device on Safe Mode with Networking. The following are the steps to take:
- From the Sign-in screen (assuming you cannot log into Windows 10/11), press and hold the Shift key while pressing the Power button.
- In the menu that opens, click Restart.
- Windows will restart with the Choose an Option Select Troubleshoot.
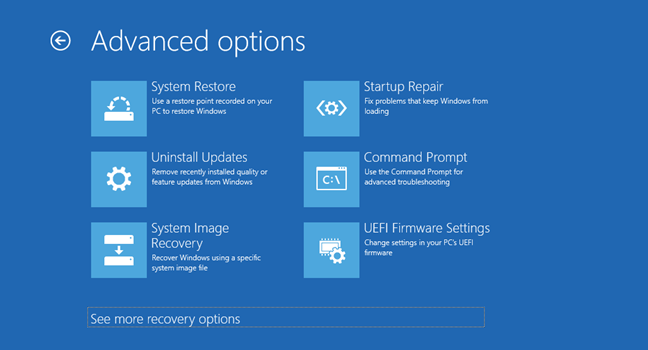
- Go to Advanced Options > Startup Settings > Restart.
- After your computer restarts, use the arrow keys to select Safe Mode with Networking or simply press the F5 key.
With Safe Mode with Networking, you can now access network resources and seek online help to remove the TeslaCrypt malware.
Once your anti-malware of choice has finished removing the TeslaCrypt malware, you still need to clean your PC with a PC repair tool or the Outbyte macAries if you are using a Mac. The reason you would want to clean your computer has to do with how the malware is spread.
Cybercriminals rely on phishing campaigns to distribute various kinds of malware. So, if your computer has been infected by the TeslaCrypt malware, there is a chance that the file, in this case the contaminated email attachment, is still somewhere on your computer, most likely in the downloads or the %Temp% folder. The PC cleaner will clear these spaces and do the additional job of repairing broken or corrupt registry entries.
Windows Recovery Options
The Windows Recovery options are a collection of repair and diagnostic tools for Windows that allow you to either refresh, reset, restore, diagnose, or repair your Windows device. It is best to use any of these tools after a nasty malware attack. Below, we shall discuss two of these Windows recovery options and explain how to use them as part of TeslaCrypt ransomware removal process.
System Restore
As the name suggests, the System Restore option lets you restore your computer to an earlier functioning state. This is achieved by undoing any changes to your computer’s settings, apps, and configuration past a certain restore point.
To get to System Restore, follow the steps leading to the Safe Mode with Networking option. But instead of clicking Startup Repair, choose System Restore.
Reset this PC
Resetting your computer reinstalls the Windows 10/11 OS, but with the choice of either keeping your files or doing away with them. Here is how to reset your computer from Settings:
- Press the Windows + I key to go the Settings app.
- Go to Update & Recovery > Recovery.
- Under the Reset this PC option, select Get Started.
- Choose to either keep or do away with your files. In case they are all encrypted by the TeslaCrypt ransomware, there is no point in keeping them.
- Follow the on-screen directions to finish the process.
How to Keep Your Computer Safe from Ransomware
While the TeslaCrypt ransomware is no longer a major threat, that doesn’t mean there are no serious ransomware threats out there. The most recent of these was the WannaCry ransomware (2017), which infected millions of computers before being stopped.
The thing about ransomware attacks is that most can be prevented by taking cybersecurity seriously. Here is a short summary of the things that you need to do to stay safe:
- Purchase an anti-malware tool and use it to regularly scan your device for malicious programs.
- Create a backup of your files so that even if you are a victim of a ransomware attack, you will still have your files available.
- Refrain from downloading email attachments that you are not sure of. It is best to take your time and check the authenticity of the emails that you receive.
- If you work from a shared office, make sure that everyone is on the same page when it comes to security.
- Do not use pirated software as it could be a source of infection.
Hopefully, this article about the TeslaCrypt ransomware has been of help to you. If you have any questions or comments, please feel free to use the comment section below.
