Are you looking for ways to securely download torrent or access the dark web? Then Tor browser might just be what you need. Tor, which is short for The Onion Router, is a secure protocol that allows you to hide your online browsing activities because of its many layers, similar to that of an onion.
How do you use this browser? How does it secure your browsing activity? What are its pros and cons? We’ll know more about it in this Tor browser review.
About the Tor Browser
Developed by the U.S. Naval Research Lab and the D.A.R.P.A., the Tor browser is an open-source software program that is designed to allow anonymous communication. This browser redirects a user’s internet traffic through different volunteer overlay networks all over the world to hide the location and browsing information from anyone doing traffic analysis.
However, unlike a virtual private network or VPN, it does not encrypt your data. Instead, it can be used alongside it. This will make it difficult for aggressive advertisers and prying eyes to track your activities online.
Expert Tip: For smoother PC performance, consider using a PC optimization tool. It handles junk files, incorrect settings, and harmful apps. Make sure it's right for your system, and always check the EULA and Privacy Policy.
Special offer. About Outbyte, uninstall instructions, EULA, Privacy Policy.
Compared to a regular browser’s incognito mode, the Tor browser offers more privacy because it obscures the IP address so users can’t be traced with it.
How the Tor Browser Works: A Closer Look
The Tor browser is designed based on the onion routing concept. In onion routing, there are layers nested one over the other, akin to an onion’s structure. These nested layers make it possible for data to be encrypted several times.
On the client-side, every layer decrypts data before it is passed to another. The final layer decrypts the innermost layer of encrypted data before it is passed to the destination.
All these layers function efficiently that IP addresses, physical locations, and other information are not revealed. This concept limits the chances of anyone to watch over your browsing activities.
While this decryption process sounds complicated, there is actually nothing to be worried about. Think of this browser simply functioning like any other browsers.
How Secure is the Tor Browser?
You may ask, is the Tor browser as secure as what the rest of the world thinks? Well, it’s not. Just like other systems, it has a few flaws and weaknesses. Because every server in the network is operated by volunteers, you can never tell where your data travels through. Still, this isn’t really a major issue because each relay can only see the location of the previous.
Also, the Tor browser is vulnerable to security attacks that are common to other browsers. So, if you are planning to use it, we suggest that you disable active scripts and plugins because they can be exploited to conceal your information.
Using the Tor Browser with a VPN
Sure, the Tor browser is already an effective tool for securing your browsing details. But it does not guarantee the same level of safety and security that VPNs do.
The good news, though, is that you need not choose between the two. It is possible to use the Tor browser and a VPN altogether.
There are two known ways to combine a VPN and this browser.
Tor over VPN
In this method, you connect to a VPN network first before you access the Tor network. There are pros to using this method. One is that it’s very easy to do. You just connect to your choice of VPN service and launch the Tor browser. That’s it.
Interestingly, some VPN services have already made this easier as they have this built-in Tor service. One popular VPN that offers this is NordVPN.
NordVPN can route your internet traffic through its secure VPN servers. After that, it directs you to the Tor network. With this setup, it’s not just your browser activity that is protected. Your device information is secured, too.
Another upside of using Tor over VPN is that all your internet data is encrypted by the VPN first before it enters the nodes of the Tor network. This means Tor’s servers cannot see your real IP address.
The downside of this method is that it won’t protect you from any malicious exit node because your traffic is already unencrypted by the time it reaches the final destination.
VPN over Tor
In this method, you establish a connection to the Tor network first before going through your VPN. Unlike the previous method, this is more complicated because in most cases, manual configuration needs to be done to the VPN network for the Tor browser to work.
The biggest advantage of using this, though, is that you stay protected from the exit nodes of the Tor network. This means your traffic does not directly go from an exit node to your destination. Rather, it is routed to a secure VPN server. That is the reason configuration is necessary for this option.
The downside of this method is that prying eyes will know that you are using the Tor network, though your activities remain hidden.
Getting Started with the Tor Browser
To connect to the Tor network, you need to do more than just installing a web browser and opening websites. You have to install a certain support code as well, which you can download from the official Tor website.
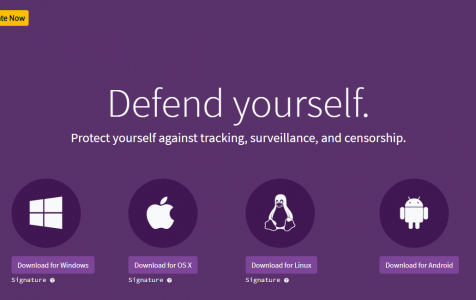
Luckily, the creators of Tor have streamlined the startup process. They created Tor browser bundles with installers that support Windows, Linux, and Mac devices. According to the Tor Project, it is best to install the browser on a USB drive to guarantee anonymity and ensure portability. This drive should have at least 80 MB of free space, though.
Now, before you can proceed with an anonymous browsing experience, you have to inform Tor about the connection you’ve established. If your connection is censored, you need to configure it first. Otherwise, you cannot access the network.
When you run the Windows installer, you will be offered the options to create a desktop shortcut or launch the browser immediately. If you can observe, the Tor browser appears like a modified version of Firefox with security plug-ins and some security tweaks design not to cache website data.
The Features of Tor Browser
Here are some of the features that many people love about the Tor browser:
- Cross-platform compatibility (supports Mac, Windows, and Linux devices)
- Data encryption before sent over the web
- Automatic data decryption at the side of the client
- Easy to use as it is a combination of the Firefox browser and the Tor Project
- Provides complete anonymity to users, servers, and websites
- Makes it possible to visit blocked websites
- Performs web-related tasks without revealing the user’s IP address
- Can route data to and from the application and service behind a firewall
- Portable (can be configured from a USB device)
- Available for x86 and x86_64 architectures
- Can handle thousands of requests and millions of users
Tor Browser Pros and Cons
Below are some of the notable pros and cons of using the Tor browser.
PROS:
- Connects to the Tor network anonymously
- Straightforward and simple interface despite the complex security protocols
- Easy to set up
- Feature-rich
- Compatible with various operating systems
- Integrated privacy tools
CONS:
- Slows down the browsing speed
- Finding local websites can be difficult
- Having no privacy features and plug-ins might confuse new users
Wrapping Up
Even with its flaws, the Tor browser is still considered an effective and powerful tool for protecting online privacy. Sure, you can always choose to use web browsers with a built-in VPN. However, know that when used alongside a VPN, one can experience the best of both worlds.
Do you know other secure web browsers that allow you to browse anonymously and protect your browsing data? Have we forgotten an important piece of information about the Tor browser? Let us know in the comments!