What is ZES Ransomware?
ZES ransomware is a malicious software program that infiltrates a system, locking the user’s data and demanding a ransom fee to unlock them. This malware is part of the Makop malware family and was first discovered in August 2020. The virus is designed to attack computer users around the world, encrypting personal items such as pictures, files, databases, documents, and many more. It uses powerful algorithms like RSA and AES to encrypt files, hence diminishing hopes of recovering the encrypted data. Each encrypted file can be seen by the victim appended with a .zes extension.
Apart from the locked data, victims are served with a ransom note titled readme-warning.txt saved on the desktop. The note explains how the perpetrators have locked data and what the victim must do to regain access. They also let the victim know that a unique key for unlocking files exists only with them and they should pay in Bitcoin currency if they wish to recover data. The note reads:
::: Greetings :::
Little FAQ:
.1.
Q: Whats Happen?
A: Your files have been encrypted and now have the “zes” extension. The file structure was not damaged, we did everything possible so that this could not happen.
.2.
Q: How to recover files?
A: If you wish to decrypt your files you will need to pay in bitcoins.
.3.
Q: What about guarantees?
A: Its just a business. We absolutely do not care about you and your deals, except getting benefits. If we do not do our work and liabilities – nobody will cooperate with us. Its not in our interests.
To check the ability of returning files, you can send to us any 2 files with SIMPLE extensions(jpg,xls,doc, etc… not databases!) and low sizes(max 1 mb), we will decrypt them and send back to you. That is our guarantee.
.4.
Q: How to contact with you?
A: You can write us to our mailbox: johncastle@msgsafe.io
.5.
Q: How will the decryption process proceed after payment?
A: After payment we will send to you our scanner-decoder program and detailed instructions for use. With this program you will be able to decrypt all your encrypted files.
.6.
Q: If I donít want to pay bad people like you?
A: If you will not cooperate with our service – for us, its does not matter. But you will lose your time and data, cause only we have the private key. In practice – time is much more valuable than money.
:::BEWARE:::
DON’T try to change encrypted files by yourself!
If you will try to use any third party software for restoring your data or antivirus solutions – please make a backup for all encrypted files!
Any changes in encrypted files may entail damage of the private key and, as result, the loss all data.
There are several distribution techniques used by ZES authors. Unfortunately, since this type of ransomware is still new, once it attacks, there is less to no hope of recovering files. Careless internet users form the majority of ZES victims since the virus orchestrators send malicious emails in bulk globally. Other techniques used to distribute ZES ransomware include:
- Software vulnerabilities
- Browser fake updates
- Insecure Wi-Fi connections
- Pirated installations
Just like any other malicious program, the ZES ransomware can be prevented by observing and practicing precautionary measures, such as ensuring the installed programs and the operating system are constantly being update, armoring your computer with a trusted anti-malware security tool, staying away from insecure websites which include torrents and pirated content distributors, and most importantly, remotely backing up all of your important files.
If your system is infected by the ZES ransomware, there is nothing you can do to recover the encrypted files. So, you should concentrate on removing the virus instead, and try other means of recovering your data from remote backups without paying the criminals.
What Does ZES Ransomware Do?
When this malicious software infiltrates the system, it modifies Windows systems, preparing it for uninterrupted file encryption. For instance, the ZES ransomware deletes Shadow Volume Copies as well as other in-built system recovery options. Such characteristics make file recovery without the decrypting key almost impossible.
To ensure that victims are pressured to pay, this ransomware targets files that are commonly used such as PDF, Microsoft Office documents (word, excel, PowerPoint, etc.), archives, and many more.
Regardless of how important the encrypted data is, at this point, it’s best to consider it as lost. We don’t advise paying even a fraction of the ransom fee to avoid further loss. Rather, take that money and invest it on a reliable security software tool to avoid a repeat in the future. Moreover, paying a ransom fee does not guarantee the return of your files. Thus, by paying, you risk losing your money in addition to the data that is already encrypted.
How to Remove ZES Ransomware
At this point, you understand that recovering files encrypted by ZES ransomware without the decryption key is nearly impossible. So, focusing on removing the virus before attempting to recover files via other means is ideal. If you have a remote backup, it’s best to get rid of the ZES ransomware first to avoid a secondary attack. This will require a reputable and trusted anti-malware software. You must first create a backup of the encrypted files using a separate, external medium. This will help you recover some, if not all of the files in the future, once a decryption tool has been released.
In most cases, after scanning the system and getting rid of the virus, the computer may experience crashes or BSODs. This can be due to the system files corrupted by the ZES ransomware. However, you don’t have to reinstall the operating system. With the help of a strong PC repair software tool, you can fix corrupted system files.
ZES Ransomware Removal Instructions
Ransomware crime is considered to be one of the most lethal cybercrimes due to its capability of locking files. It is dangerous and destructive in all sorts of levels such that one has to act accordingly once they notice it in their system. Apart from locking files, it can also damage your system to a point of paying an arm and leg to get it fixed.
We emphasize on not tolerating the idea of paying the ransom fee because even if you get the files back, criminals already have access to your system and can repeat the same attack in the future. The ZES ransomware uses a symmetric and an asymmetric encryption technique, making it impossible to recover data without the key that is in possession of the cybercriminals.
To get rid of the ransomware, here are the options that you have:
- Try out third-party tools that can hopefully recover a fraction of the encrypted files from the storage drive.
- Make use of the automated Windows backup systems like the Windows Previous Versions to try and recover data.
- Make a copy of the encrypted data, and then wait for security researchers to release a decrypting tool (note that the timeframe may vary from months to years).
Taking everything into consideration, here is a step by step process to removing the ZES ransomware from your system permanently. Remember to have a copy of the encrypted files before executing this removal procedure:
To delete ZES Ransomware from your device, follow the steps below:
Step 1. Remove ZES Ransomware from Windows
Step 2. Delete ZES Ransomware from Mac OS X
Step 3. Get rid of ZES Ransomware from Internet Explorer
Step 4. Uninstall ZES Ransomware from Microsoft Edge
Step 5. Delete ZES Ransomware from Mozilla Firefox
Step 6. Remove ZES Ransomware from Google Chrome
Step 7. Get rid of ZES Ransomware from Safari
How to Remove ZES Ransomware from Windows
One of the common traits of ZES Ransomware is that they like to pose as legitimate programs or can be bundled with legitimate programs in order to infect your computer. The first thing you need to do when faced with the risk of a ZES Ransomware is to uninstall the program that came with it.
To remove potentially malicious and unwanted programs from Windows and get rid of the ZES Ransomware permanently, follow these instructions:
1. Uninstall malicious programs.
Click on Start, then type in Control Panel in the search box. Click Control Panel from the search results, then click on the Uninstall a program link under Program. The Control Panel looks the same for Windows 7 computers, but for Windows XP users, click on Add/Remove Programs instead.
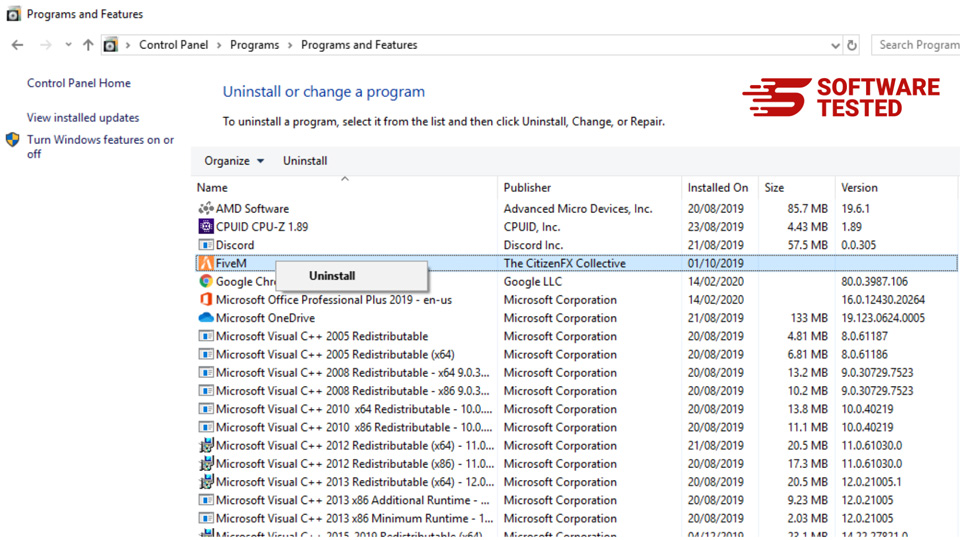
For Windows 10/11 users, you can also uninstall programs by navigating to Start > Settings > Apps > Apps & features.
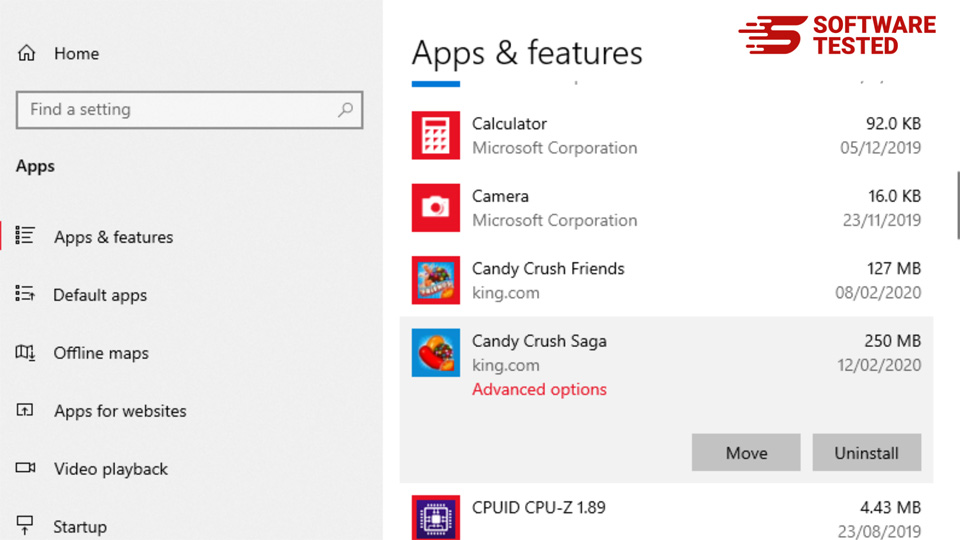
In the list of programs on your computer, look for recently installed or suspicious programs that you suspect to be malware.
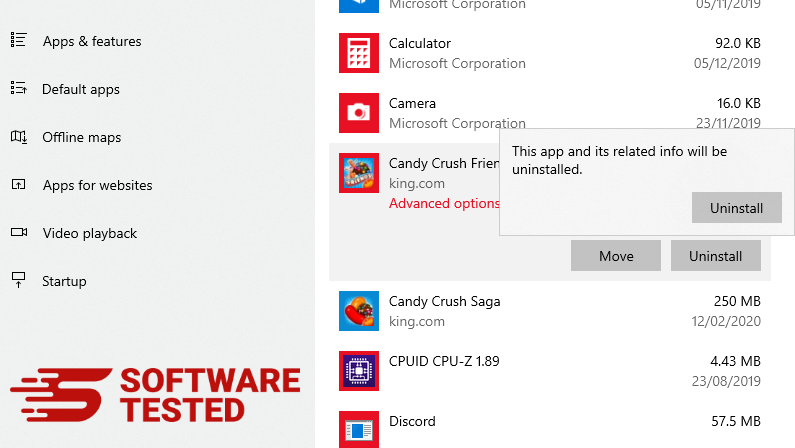
Uninstall them by clicking (or right-clicking if you’re in the Control Panel), then choose Uninstall. Click Uninstall once again to confirm the action. Wait for the uninstallation process to be completed.
3. Remove ZES Ransomware from Windows shortcuts.
To do this, right-click on the shortcut of the program you uninstalled, then select Properties.
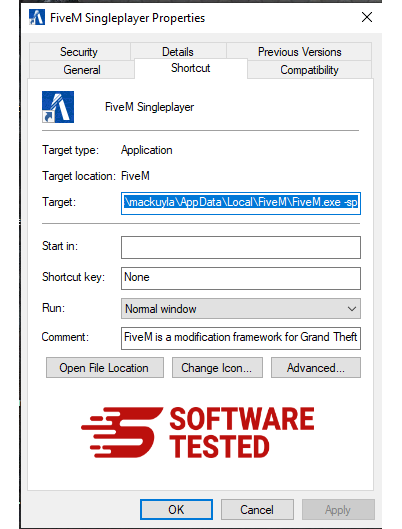
It should automatically open the Shortcut tab. Look at the Target field and delete the target URL that is related to the malware. This URL points to the installation folder of the malicious program you uninstalled.
4. Repeat all the steps listed above for all the program’s shortcuts.
Check all locations where these shortcuts might be saved, including the Desktop, Start Menu, and the Taskbar.
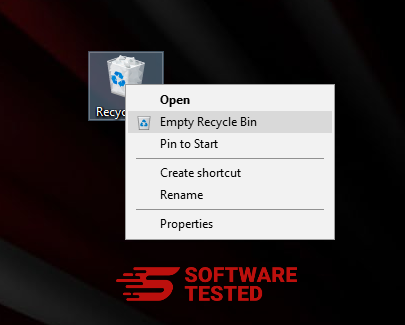
5. Empty the Recycle Bin.
Once you have deleted all the unwanted programs and files from Windows, clean up your Recycle Bin to completely get rid of the ZES Ransomware. Right-click on the Recycle Bin on your Desktop, then choose Empty Recycle Bin. Click OK to confirm.
How to Delete ZES Ransomware from macOS
macOS is more secure than Windows, but it is not impossible for malware to be present on Macs. Just like other operating systems, macOS is also vulnerable to malicious software. In fact, there have been several previous malware attacks targeting Mac users.
Deleting ZES Ransomware from a Mac is a lot easier than other OS. Here’s the complete guide:
- If you suspect a recently installed software to be malicious, uninstall it immediately from your Mac. On Finder, click the Go > Applications. You should see a list of all the apps currently installed on your Mac.
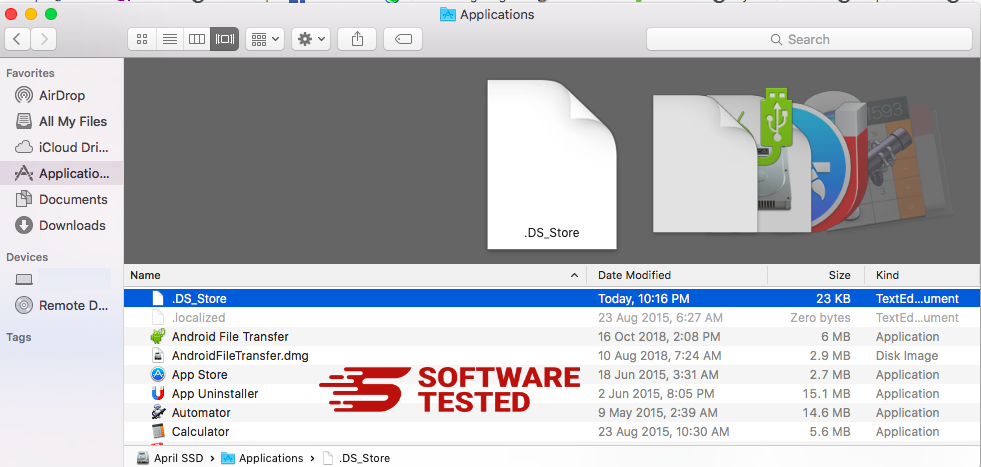
- Find the app associated with ZES Ransomware or other suspicious apps you want to delete. Right-click on the app, then choose Move to Trash.
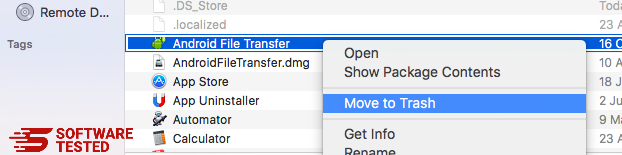
To completely get rid of ZES Ransomware, empty your Trash.
How to Get Rid of ZES Ransomware from Internet Explorer
To ensure that the malware that hacked your browser is completely gone and that all unauthorized changes are reversed on Internet Explorer, follow the steps provided below:
1. Get rid of dangerous add-ons.
When malware hijacks your browser, one of the obvious signs is when you see add-ons or toolbars that suddenly appear on Internet Explorer without your knowledge. To uninstall these add-ons, launch Internet Explorer, click on the gear icon at the top-right corner of the browser to open the menu, then choose Manage Add-ons.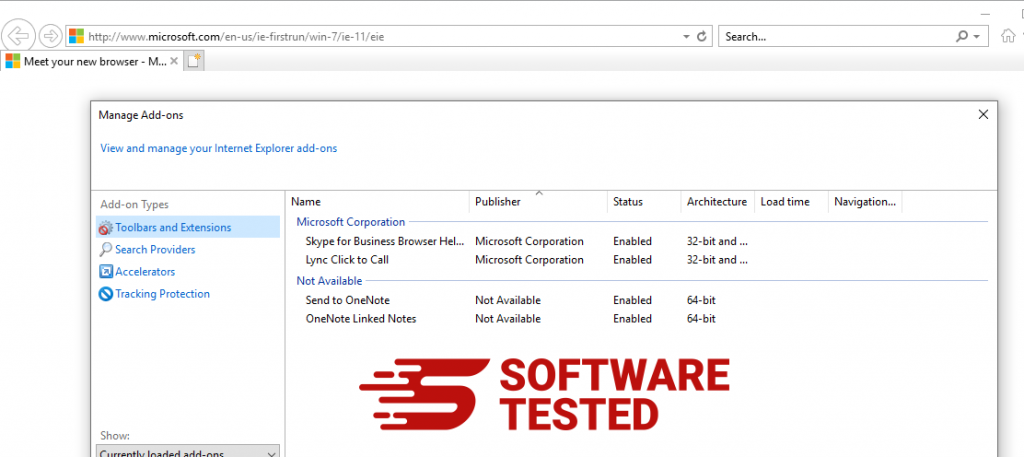
When you see the Manage Add-ons window, look for (name of malware) and other suspicious plugins/add-ons. You can disable these plugins/add-ons by clicking Disable.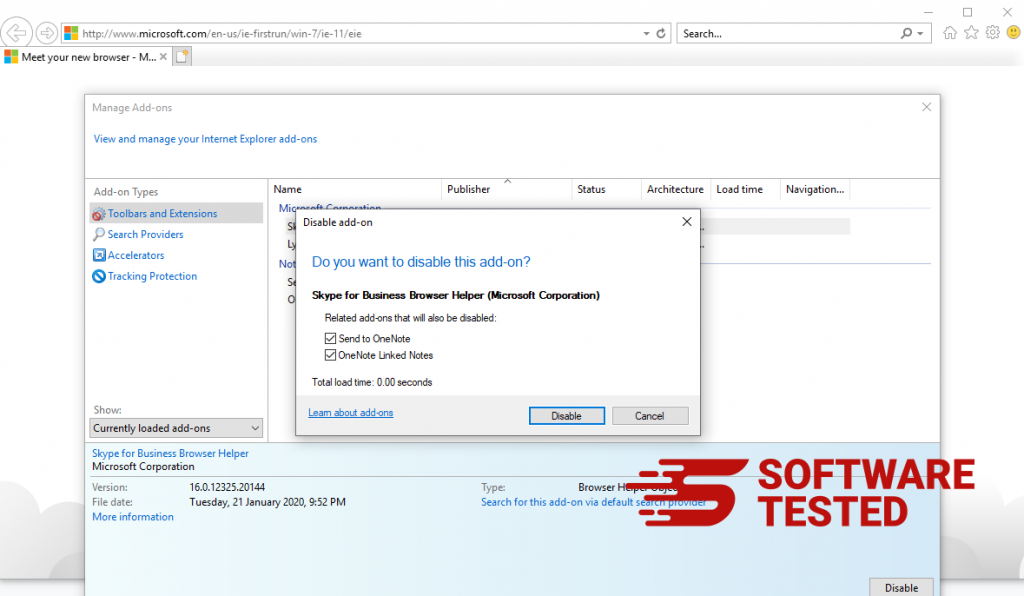
2. Reverse any changes to your homepage caused by the malware.
If you suddenly have a different start page or your default search engine has been changed, you can change it back through the Internet Explorer's settings. To do this, click on the gear icon at the upper-right corner of the browser, then choose Internet Options.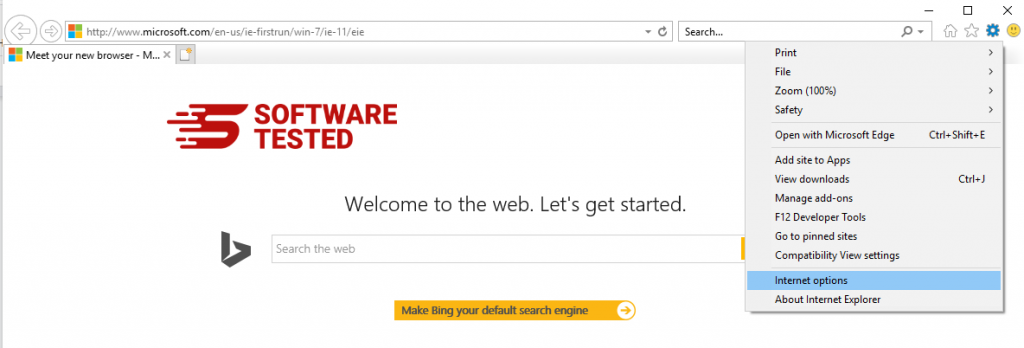
Under the General tab, delete the homepage URL and enter your preferred homepage. Click Apply to save the new settings.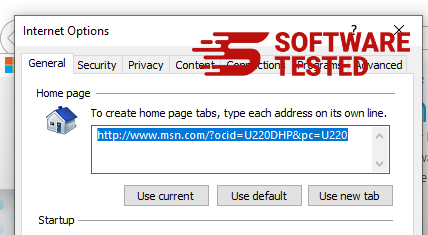
3. Reset Internet Explorer.
From the Internet Explorer menu (gear icon at the top), choose Internet Options. Click on the Advanced tab, then select Reset.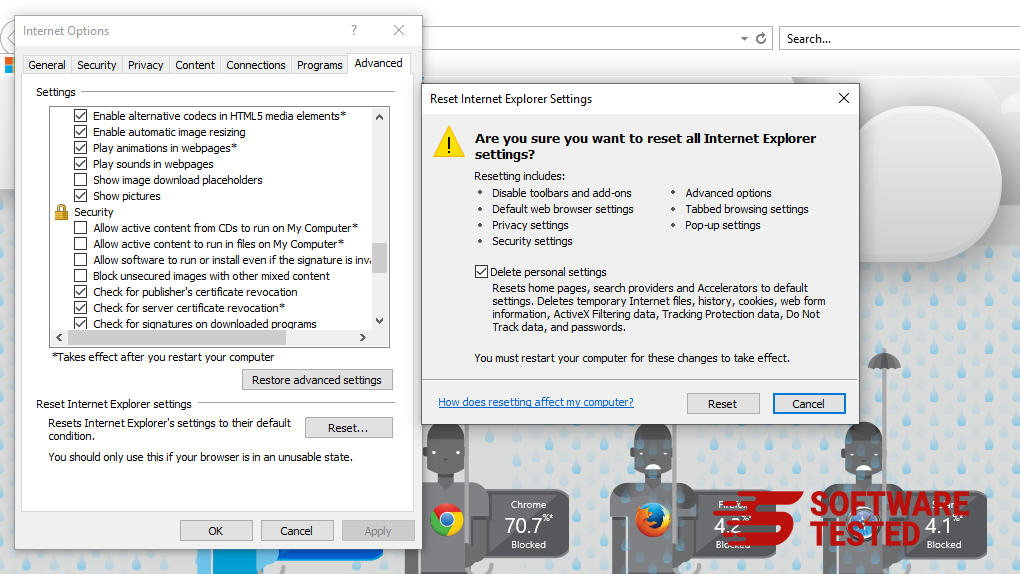
In the Reset window, tick off Delete personal settings and click the Reset button once again to confirm the action.
How to Uninstall ZES Ransomware on Microsoft Edge
If you suspect your computer to have been infected by malware and you think that your Microsoft Edge browser has been affected, the best thing to do is to reset your browser.
There are two ways to reset your Microsoft Edge settings to completely remove all the traces of malware on your computer. Refer to the instructions below for more information.
Method 1: Resetting via Edge Settings
- Open the Microsoft Edge app and click More or the three-dot menu located at the upper-right corner of the screen.
- Click Settings to reveal more options.
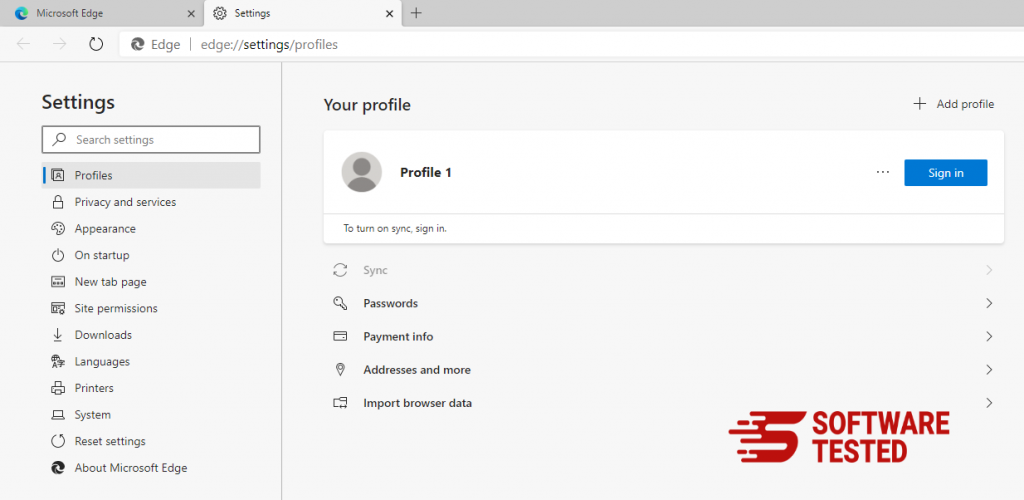
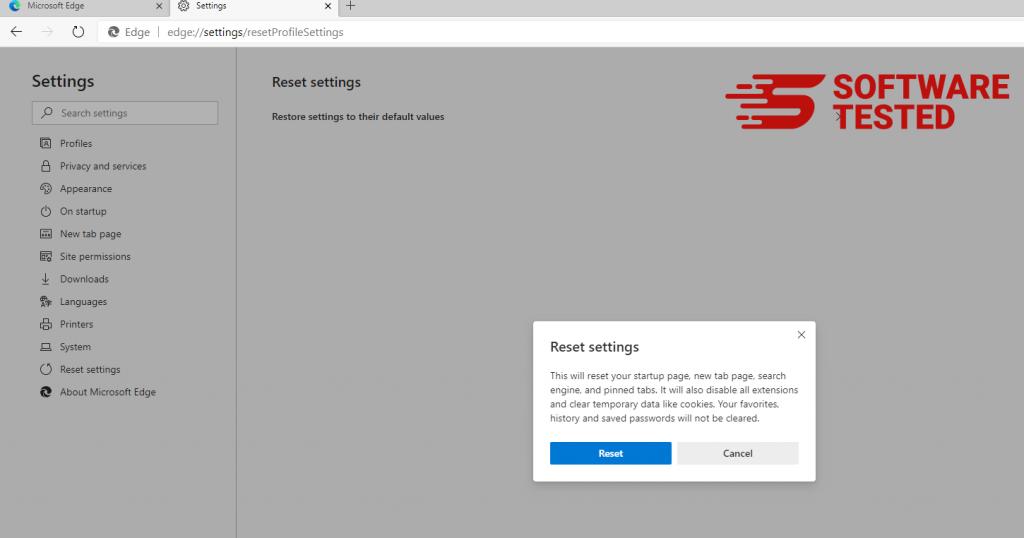
- In the Settings window, click Restore settings to their default values under Reset settings. Click the Reset button to confirm. This action will reset your browser’s startup page, the new tab page, default search engine, and pinned tabs. Your extensions will also be disabled and all temporary data like cookies will be deleted.
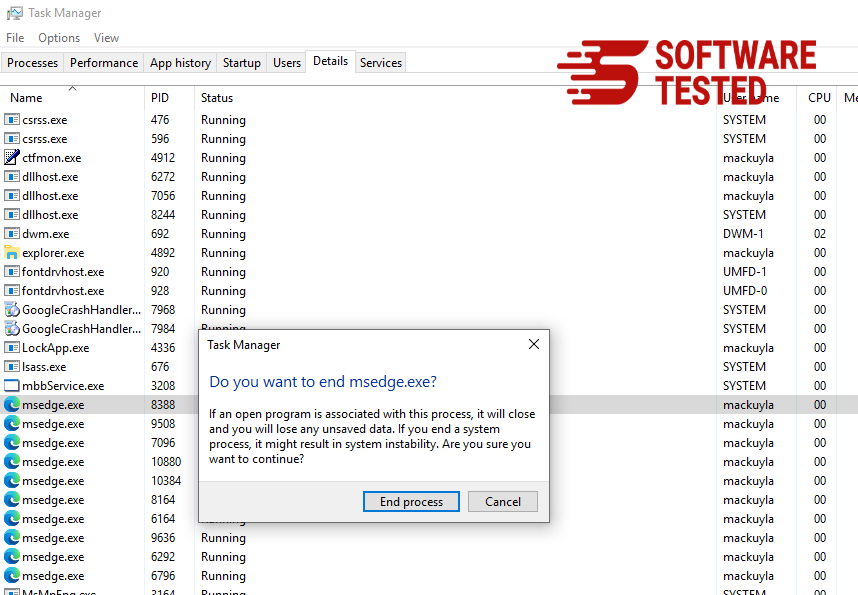
- Afterwards, right-click on the Start menu or the Windows logo, then select Task Manager.
- Click on the Processes tab and search for Microsoft Edge.
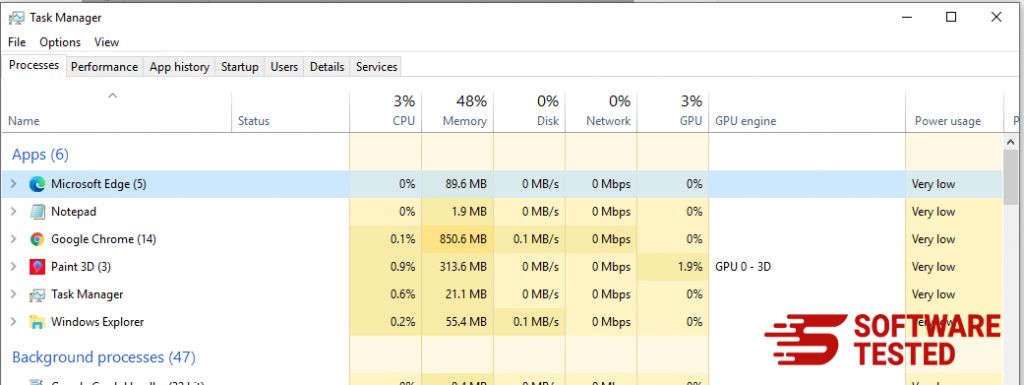
- Right-click on the Microsoft Edge process and select Go to details. If you don't see the Go to details option, click More details instead.
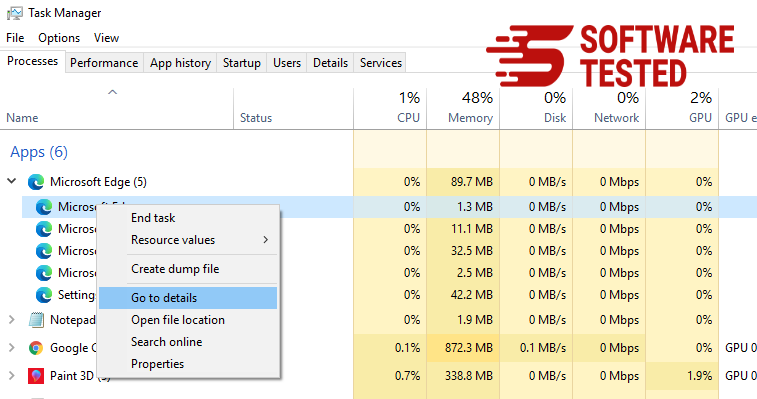
- Under the Details tab, look for all the entries with Microsoft Edge in their name. Right-click on each of these entries and choose End Task to quit those processes.
- Once you have quit all those processes, open Microsoft Edge once again and you'll notice that all the previous settings have been reset.
Method 2: Resetting via Command
Another way to reset Microsoft Edge is by using commands. This is an advanced method that is extremely useful if your Microsoft Edge app keeps crashing or won't open at all. Make sure to back up your important data before using this method.
Here are the steps to do this:
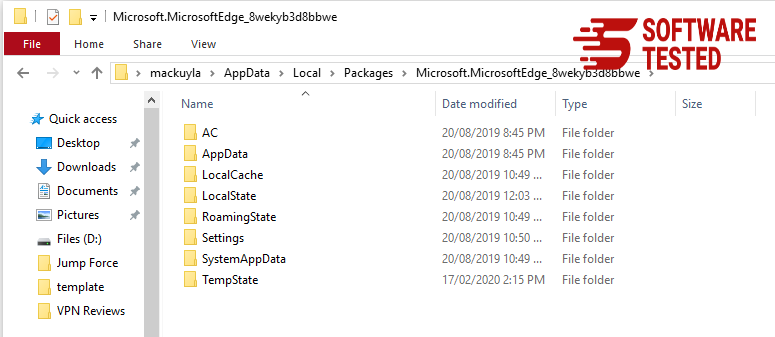
- Navigate to this folder on your computer: C:\Users\%username%\AppData\Local\Packages\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
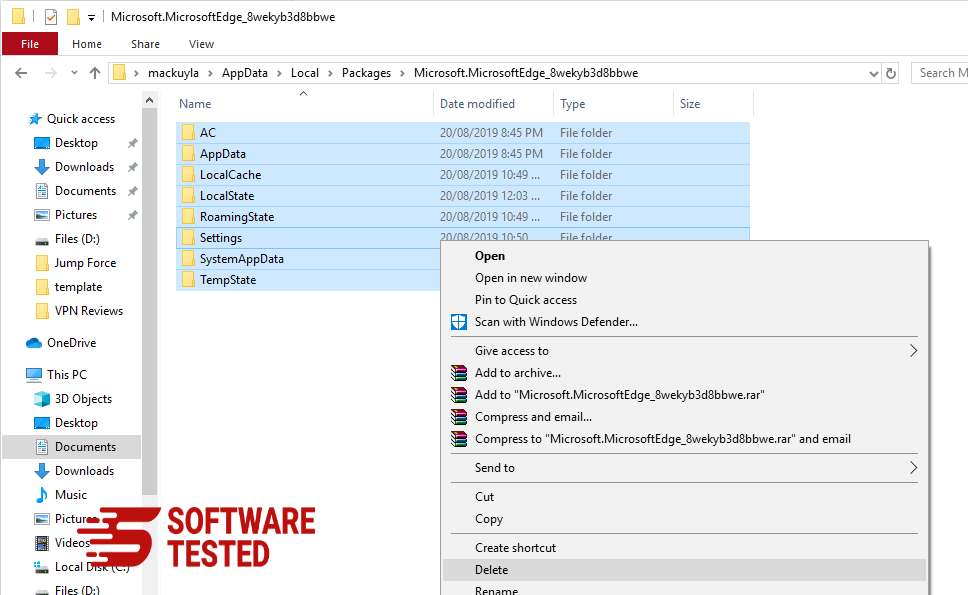
- Select everything inside the folder, right-click on the highlighted files, then click Delete from the options.
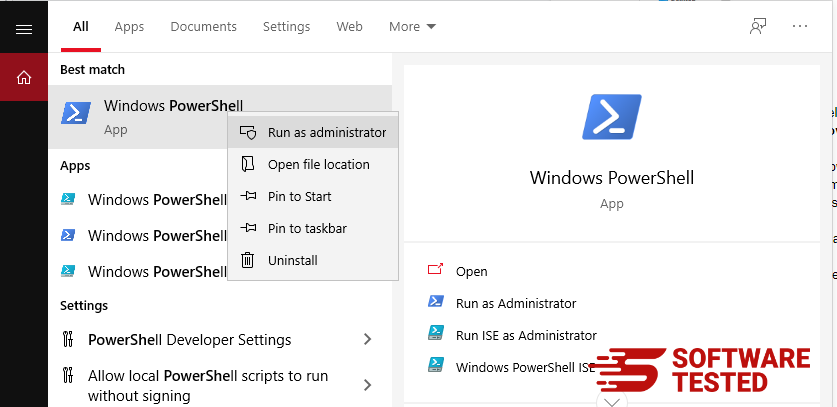
- Search for Windows PowerShell using the search box beside the Start menu.
- Right-click on the Windows PowerShell entry, then choose Run as administrator.
- In the Windows PowerShell window, type in this command:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register $($_.InstallLocation)\AppXManifest.xml -Verbose}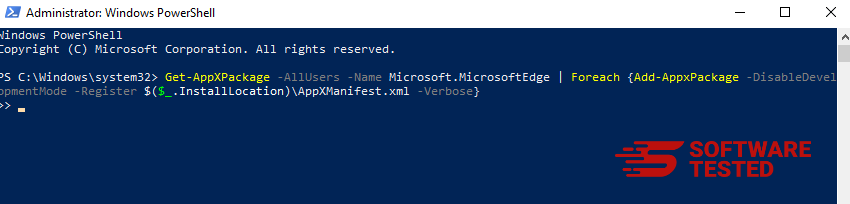
- Press Enter to execute the command.
- Once the reset process has been completed, ZES Ransomware should be completely deleted from your Microsoft Edge browser.
How to Delete ZES Ransomware from Mozilla Firefox
Just like other browsers, malware tries to change the settings of Mozilla Firefox. You need to undo these changes to remove all traces of ZES Ransomware. Follow the steps below to completely delete ZES Ransomware from Firefox:
1. Uninstall dangerous or unfamiliar extensions.
Check Firefox for any unfamiliar extensions that you don't remember installing. There is a huge chance that these extensions were installed by the malware. To do this, launch Mozilla Firefox, click on the menu icon at the top-right corner, then select Add-ons > Extensions.
In the Extensions window, choose ZES Ransomware and other suspicious plugins. Click the three-dot menu beside the extension, then choose Remove to delete these extensions.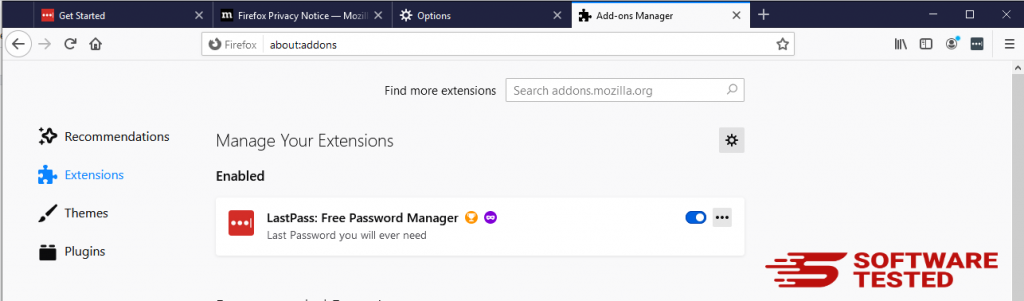
2. Change your homepage back to default if it was affected by malware.
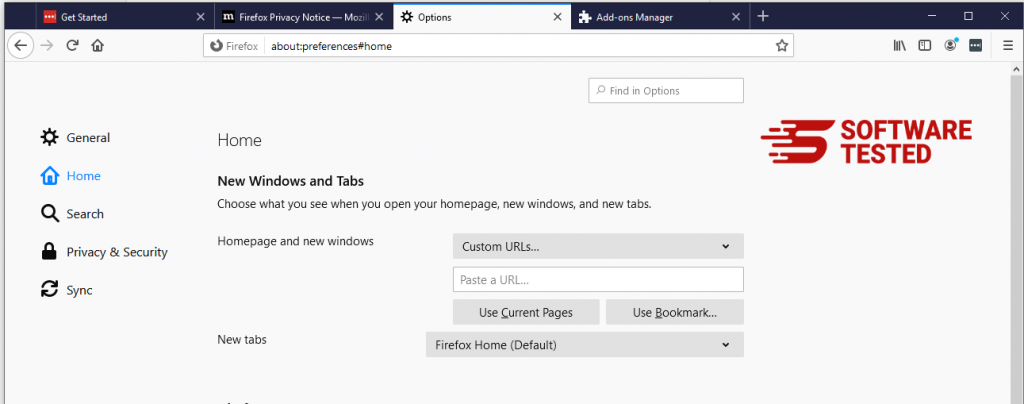
Click on the Firefox menu at the upper-right corner of the browser, then choose Options > General. Delete the malicious homepage and type in your preferred URL. Or you can click Restore to change to the default homepage. Click OK to save the new settings.
3. Reset Mozilla Firefox.
Go to the Firefox menu, then click on the question mark (Help). Choose Troubleshooting Information. Hit the Refresh Firefox button to give your browser a fresh start.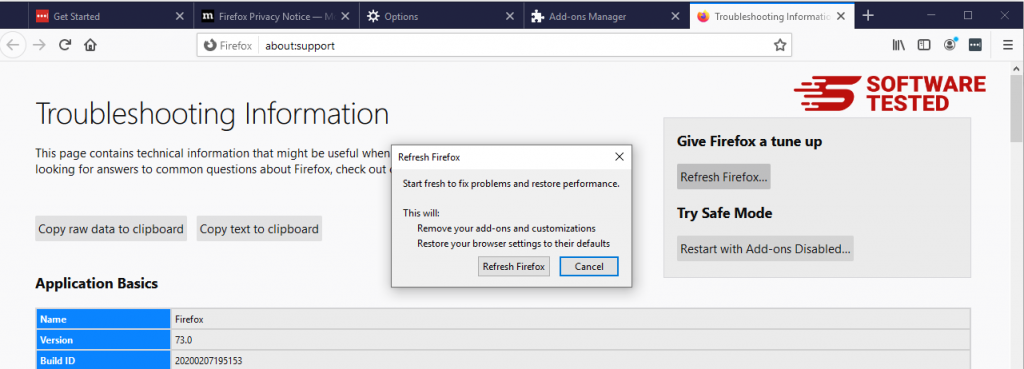
Once you’ve completed the steps above, ZES Ransomware will be completely gone from your Mozilla Firefox browser.
How to Remove ZES Ransomware from Google Chrome
To completely remove ZES Ransomware from your computer, you need to reverse all of the changes on Google Chrome, uninstall suspicious extensions, plug-ins, and add-ons that were added without your permission.
Follow the instructions below to remove ZES Ransomware from Google Chrome:
1. Delete malicious plugins.
Launch the Google Chrome app, then click on the menu icon at the upper-right corner. Choose More Tools > Extensions. Look for ZES Ransomware and other malicious extensions. Highlight these extensions you want to uninstall, then click Remove to delete them.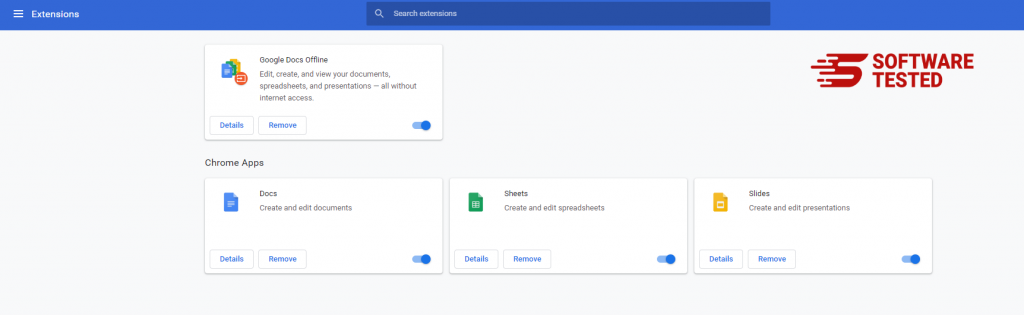
2. Revert changes to your homepage and default search engine.
Click on Chrome's menu icon and select Settings. Click On Startup, then tick off Open a specific page or set of pages. You can either set up a new page or use existing pages as your homepage.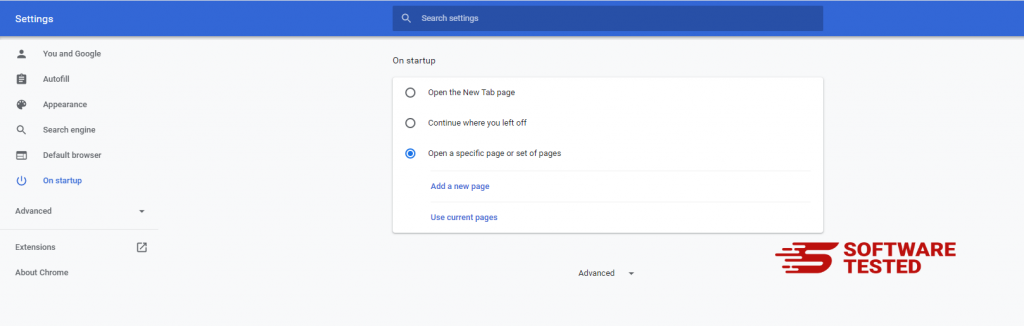
Go back to Google Chrome's menu icon and choose Settings > Search engine, then click Manage search engines. You'll see a list of default search engines that are available for Chrome. Delete any search engine that you think is suspicious. Click the three-dot menu beside the search engine and click Remove from list.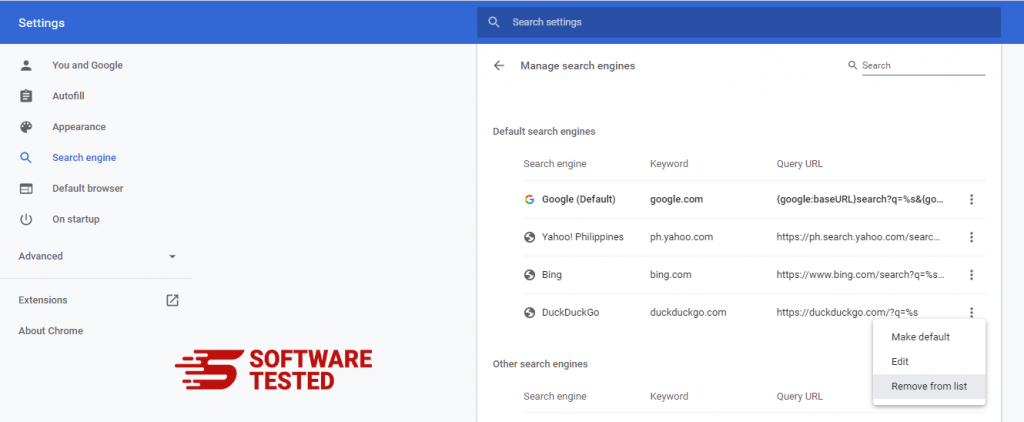
3. Reset Google Chrome.
Click on the menu icon located at the top right of your browser, and choose Settings. Scroll down to the bottom of the page, then click on Restore settings to their original defaults under Reset and clean up. Click on the Reset Settings button to confirm the action.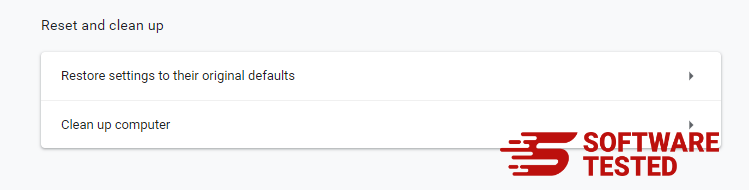
This step will reset your startup page, new tab, search engines, pinned tabs, and extensions. However, your bookmarks, browser history, and saved passwords will be saved.
How to Get Rid of ZES Ransomware from Safari
The computer’s browser is one of the major targets of malware — changing settings, adding new extensions, and changing the default search engine. So if you suspect your Safari to be infected with ZES Ransomware, these are the steps you can take:
1. Delete suspicious extensions
Launch the Safari web browser and click on Safari from the top menu. Click Preferences from the drop-down menu.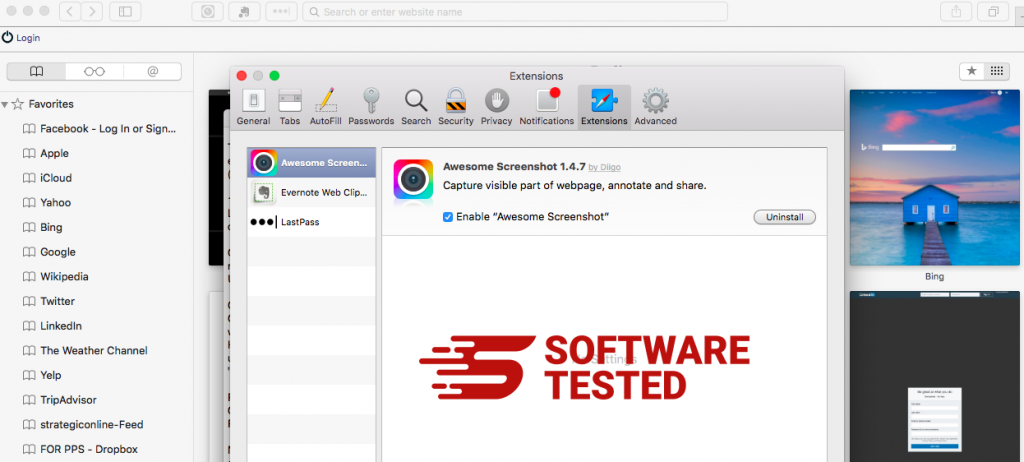
Click on the Extensions tab at the top, then view the list of currently installed extensions on the left menu. Look for ZES Ransomware or other extensions you don’t remember installing. Click the Uninstall button to remove the extension. Do this for all your suspected malicious extensions.
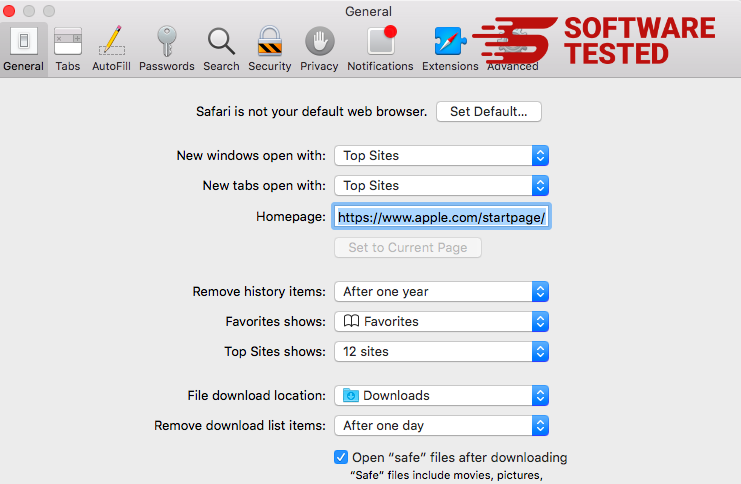
2. Revert changes to your homepage
Open Safari, then click Safari > Preferences. Click on General. Check out the Homepage field and see if this has been edited. If your homepage was changed by ZES Ransomware, delete the URL and type in the homepage you want to use. Make sure to include the http:// before the address of the webpage.
3. Reset Safari
Open the Safari app and click on Safari from the menu at the upper-left of the screen. Click on Reset Safari. A dialog window will open where you can choose which elements you want to reset. Next, click the Reset button to complete the action.
