The Rezm ransomware is a malware that encrypts all the files on a computer and demands that victims pay a ransom of $980 in the form Bitcoins to access their files again. The Bitcoin address, to which the ransom is to be sent, is mentioned in a readme.txt file. This file also asserts that a single file will be decrypted for free as a proof of their intention to restore access. Victims who are able to pay the ransom within 72 hours are also guaranteed a 50% discount on the ransom price.
What Can the Rezm Ransomware Do?
The Rezm virus is similar to other well-known ransomware such as Nppp, Mool, and Ooss that also encrypt files and demand ransom payments in the form of Bitcoins. Because the Rezm malware normally encrypts files using an AES-256 encryption algorithm, it is virtually impossible to recover the files without paying the ransom. The cybercriminals behind the malware also point this out in their readme.txt.
How Did the Rezm Ransomware Infect Your Computer?
The ransomware mainly spreads through email phishing campaigns. When a victim downloads an attachment, or clicks a link contained in these emails, they unwittingly unleash the ransomware. Your computer can also get infected if you visit unsecure sites or when you download software from untrusted sources.
How to Know if my Computer is Infected with the Rezm Ransomware
What are the signs of infection by the Rezm ransomware? It is actually very easy to tell if your computer has been infected by the Rezm malware. The most glaring sign is the fact that all the encrypted files will have a .rezm file extension. As an example, if there is a Word document titled mydocument.docx, it will be converted to mydocument.docx.rezm.
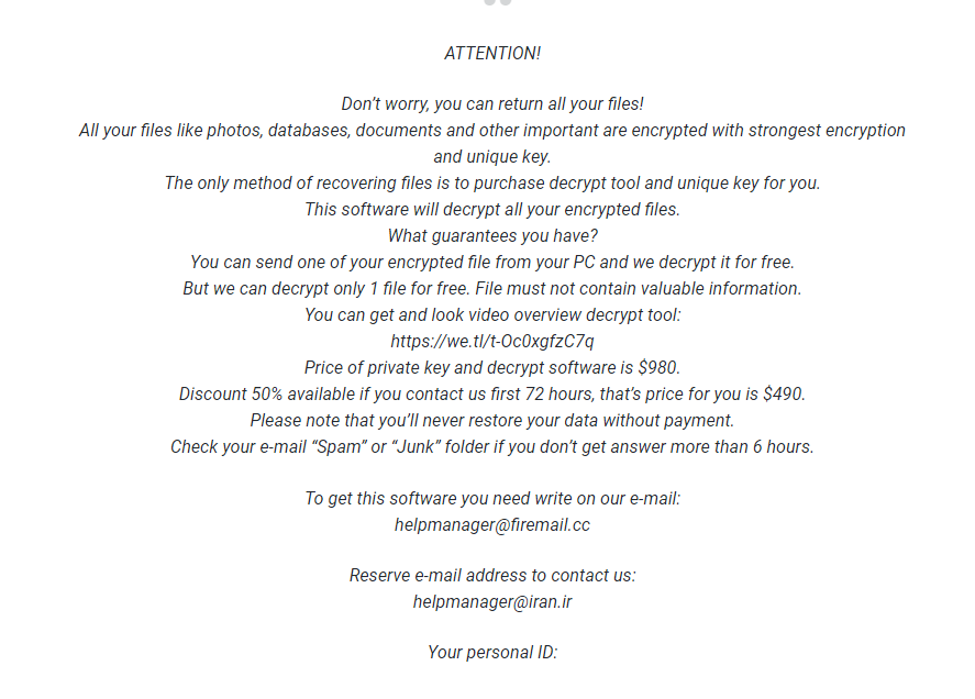
The Rezm ransomware leaves behind a unique readme.txt file. This document includes a notification about the encrypted files, a contact address, the ransom amount of $980, and a statement promising to decrypt your files once the ransom has been paid. Here is a screenshot of the readme.txt message left behind by the Rezm malware.
How to Remove the Rezm Ransomware
Before discussing ways of removing the Rezm malware from your computer, let us first point to the elephant in the room. Should you pay the ransom? $980 is after all a small amount considering the extensive loss that the ransomware might cause to a small organization, or office that stores client files on their computers.
It is important to note that it is generally recommended not to pay the ransom, despite how desperate the situation may seem. Doing so may encourage the cybercriminals behind the malware to continue targeting individuals or organizations similar to yours. Not to mention, you can never really trust fraudsters to keep their word on the matter of decrypting your files after you pay the ransom. They are criminals for a reason. Lastly, but perhaps most importantly, even if you pay the ransom, you still have not dealt with the security flaws that led to your computer being infected in the first place. Other ransomware families may be waiting to strike now that you have demonstrated your willingness to pay.
Eliminating the Rezm Ransomware with an Antivirus Software
The files and folders that power the Rezm malware are usually deeply embedded on the victim’s computer, a reason that necessitates the use of a powerful anti-malware solutions such as Outbyte Antivirus. The software will remove all malicious programs and their registry keys, thus totally eliminating the threat that they pose. It will also prevent future infiltration attempts by staying vigilant.
That said, it is worth noting that the antivirus is not a decrypting tool and that while it will help get rid of the Rezm malware, it will not recover your files for you. File recovery is only possible if you have shadow copies available.
Apart from an antivirus, you might also want to download a PC repair tool that will delete junk files, repair broken or corrupt registry entries, monitor the performance of your apps, and make the process of deleting problematic apps easier. Deleting junk files and clearing your browser history is especially important because it eliminates the spaces that malware entities are known to hide.
You might be wondering if there are other ways of getting rid of the malware that don’t involve using an antivirus tool or a PC cleaner. Yes, there are. Windows has excellent recovery tools such as System Restore and the PC reset option, all of which you can use to remove problematic apps.
System Restore
System Restore is a Windows recovery process that will revert any changes to your computer past a certain restore point. The restore point is like a “snapshot” of the OS, apps, and settings at a point in time. To get to the system restore option, take the following steps:
- On the windows search box, type “create a restore point”.
- On the System Properties app, go to the System Protection tab and click System Restore.
- Choose a restore point from the list of restore points available on your computer.
- Follow the on-screen directions to complete the process.
You can also access the System Restore option from a black-screen, but that won’t be necessary when it comes to the Rezm malware because it does not prevent you from accessing Windows apps and settings. The other Windows recovery process that you can use to get rid of the malware is resetting your computer. None of these processes will recover your files, however, but they will nonetheless get rid of the malware for you.
