Ransomware is a harmful virus that attacks devices preventing victims from accessing their files. The locked files get encrypted and remain in the computer in a non-readable state. Decrypting these files requires a special key that is in the possession of the perpetrators. To get the key, a ransom fee should be paid for.
Currently, a lot of users are feeling the effects of Google Ransomware (Phobos), which according to them, infects computers through file-sharing sites and dubious emails. Once it reaches the host computer, the malware encrypts the files. And then, the perpetrators demand payment in the form of a ransom fee.
About Google Ransomware (Phobos)
The Google Ransomware (Phobos), a member of the ill-famed Phobos ransomware family, is a cryptovirus that has no connection to the tech giant, Google LLC. In exchange for the decryption key, the victims are forced to pay a cryptocurrency fee to the cybercriminals. This is a model used by almost all ransomware entities out there.
What Does Google Ransomware (Phobos) Do?
When Google Ransomware (Phobos) infiltrates your system, it encrypts files like all ransomware entities do. And then, it adds a 3-part extension to all your personal files that include a unique victim’s ID, the contact details (email) of the cybercriminals, and a .google extension. After completing file encryption, the files become inaccessible unless decoded.
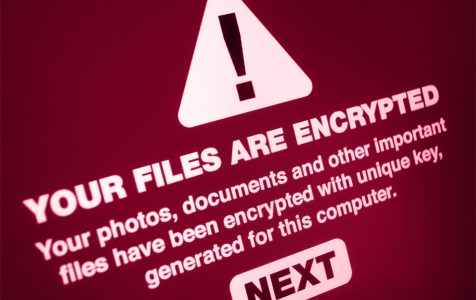
When the ransomware successfully infiltrates a system, it creates two types of ransom notes. These are usually dropped to the victim’s device in the form of a .txt file and a pop-up window.
Note that a ransomware entity does not attack system files. It only targets personal files such as videos, images, and documents. These are things that are likely to be valuable to the victim. Because of this, it is easy for cybercriminals to convince affected users to pay the ransom.
The .txt ransom note read as follows:
!!!All of your files are encrypted!!!
To decrypt them send e-mail to this address: jackbez@yeah.net
The pop-up window ransom note read as follows:
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail jackbez@yeah.net
Write this ID in the title of your message –
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment, we will send you the tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 4Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click ‘Buy bitcoins’, and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
The perpetrators generally send an enticing offer to prove that they can unlock your files and convince you as the victim to give in to their demands. They offer to decrypt up to 5 files for free. They don’t specify the ransom fee which means it varies depending on how they size your financial status. Whatever the cost may be, the affected user will have to pay them in Bitcoin. This is safer for them as they cannot be traced. We are against paying any amount as this may lead to financial stresses. Moreover, there is no guarantee that you will get your files back.
People who pay the ransom fee are likely to fall victims again in future. The perpetrators keep records of whom they have attacked. After seeing that they could persuade you into paying their demands, they retreat. And then, they make plans to attack you again in the future.
How to Remove Google Ransomware (Phobos)
Unfortunately, encrypted files cannot be decrypted without the key. So, you should avoid paying for any tools that claim they can decrypt the encrypted files to avoid further loss. It’s best to have a backup of the encrypted files and consider them as lost for now. Then, you can start the removal process of Google Ransomware (Phobos).
There are a few measures to apply when your system gets infected with ransomware entities like Google Ransomware (Phobos). Some of them are as follows:
- Isolate the affected device. This requires disconnecting the device from the internet. Then, don’t plug any external hardware storage to the system. You must log out of all your cloud accounts using a different device.
- The best way to win combat is to know who you’re fighting against. You must identify the ransomware from the extension or email. This will help you know how to handle the malware without further loss.
- Check for free ransomware decryption tools. Avoid paid ones at all costs. The idea is not to give in to the demands of criminals. Spending a dime on a decrypting tool means the criminals have forcefully made you spend. Also, there is no guarantee the decryption tool will work. Try out free decryption tools to check if any of them can help get you back the files.
- Restore data using a third-party file recovery tool. Depending on the ransomware quality, you may recover some of the lost files using a strong recovery tool.
Conclusion
The best way to fight ransomware is to know the tactics used by cybercriminals. This way, you stay safe from their means of spreading malware. The tactics they use include spam emails, insecure downloads, bundled installation, as well as dubious ads.
There are many more tactics used by criminals to infect their targets. So, it’s important to keep a strong anti-malware security suite. Have it running in the background, and thus avoid any attacks.