As the world is looking for ways to defeat the coronavirus, cybercriminals are taking advantage of everyone’s thirst for information to spread malware entities through phishing campaigns and the promotion of malicious websites.
Coronavirus-themed cyberattacks are many and they take different forms, depending on the goal of the attackers. In some cases, cybercriminals create fake Android, Windows, and iOS apps that purport to show the ‘map of Corona virus’, while other apps offer to give up-to-date news on the spread of the virus. These phony apps then encrypt the victim’s data and demand a ransom payment of about $45.
The main distributer of the CoranaVirus ransomware is coronavirusapp[.]site. Once the victim visits this site, they will be prompted to download the fake coronavirus tracking app that promises among other things to “give them access to a coronavirus map tracker that appears to provide tracking and statistical information about COVID-19, including heatmap visuals.”
When a victim downloads the fake coronavirus app, they are essentially installing a malicious file ‘WSHSetup.exe’ which is usually pre-programmed to download other malware entities, including the notorious KPot stealer. KPot, also known as Khalesi, is an information stealer and will forage for passwords, cookies, payment information, user details, system information, physical location, and any other useful piece of data that it can get its hands on.
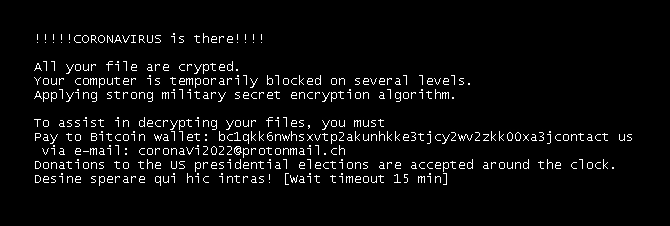
Only after downloading the KPot stealer does the ‘WSHSetup.exe’ perform the coronavirus ransomware execution. The ransomware will encrypt the victim’s data and demand a ransom amount of $45 or the equivalent of 0.008 Bitcoins.
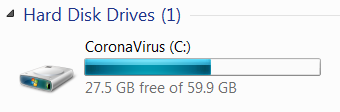
If the ransomware manages to infect a Windows PC, the ransomware will encrypt all the victim’s files, delete shadow copy backups and change their name to coronaVi2022@protonmail.ch___%file_name%.%ext%. It will also rename the C drive to CoronaVirus C as seen below.
To display the ransom note, the malware entity will take the extra step of modifying the BootExcute key on HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager. The ransom note seen below will display for about 15 minutes before the Windows OS is loaded.
The $45 ransomware amount demanded by the cybercriminals is atypical for a ransom amount as the normal ransomware payout is usually $400 and above. Perhaps, the malware creators want as many people as possible to pay the ransomware.
First things first, should you pay the ransom amount? After all, $45 is not a lot of money now, is it? On this cybersecurity blog, we have severally warned against the paying of ransom no matter how lenient the ransom terms and conditions are. Because think about it, if cybercriminals are allowed to profit from the dire situation that the coronavirus pandemic has put us all in, they will not hesitate in the slightest to exploit another catastrophe. In other words, the sooner we break the cycle, the better it is for everyone. At the same time, you cannot really trust the malware creators to keep their word as their motivation is not honorable to begin with.
Now that that’s out of the way, how do you actually remove the Coronavirus ransomware? For this, you will need a powerful anti-malware solution such as Outbyte Anti-Malware. It is capable of performing a deep cleanse of your device and delete all malware entities.
Most anti-malware software including Outbyte Antivirus work best when the computer is run on Safe Mode with Networking. The networking part means that you will be able to access network resources such as the internet which you can then use to download utility apps and seek further help on the matter of removing the coronavirus ransomware.
To run your Windows 10/11 device on Safe Mode with Networking, take the following steps:
- Log out of your out your Windows 10/11 device and as soon as you see the Sign In screen, press the Shift key on the keyboard and tap the Power button.
- On the Choose an option screen that appears once your device restarts, select Troubleshoot.
- Under the Troubleshoot options, select Advanced options > Startup Settings.
- Click Restart.
- After your computer restarts, use the arrow keys to select Safe Mode with Networking. Alternatively, press the F5 key.
The second step in the removal of the coronavirus ransomware is to use a PC repair tool to clear your computer of junk files and broken registry errors, and to optimize startup items.
Other Removal Options
While we highly recommend that you use an anti-malware software, it is not the only option that you have when it comes to deleting the coronavirus ransomware as you can manually track down the virus and eliminate it. There are two ways to do this. The first involves using the Task Manager.
- Press the Ctrl, Alt, and Delete buttons on your computer to get to the Windows security options.
- Choose Task Manager.
- Go the Processes tab and look for ‘WSHSetup.exe’ process.
- Right-click to End task.
- Right-click again to Open file location.
- Go to the file location and delete all the files and folders.
- Now, go to the Downloads folder and delete the original installer.
To make sure that the virus has completely been removed from your computer, now deploy a Windows recovery tool such as System Restore or the Reset this PC option.
How to Avoid COVID-19 Scams
So that you do not fall victim to any Covid-19 scams in the future, find a reliable news source, such as the BBC, a medical journal, or a reputable university to get all your Covid-19 updates.
Also, take the time to learn about the nature of the virus, how it is spread, the risk factors as the more you learn about it, the less likely you are to fall victim to scams.
