There are millions of apps available on the Google Play Store, but as previous Android-related security crises have shown, not all apps in there are safe and secure. The Play Store is increasingly becoming notorious for hosting fake apps, with several batches of them discovered over the years.
These fake apps could either be harmless adware or malicious malware that can steal user information. Last April, fake Android apps designed for targeted surveillance were discovered by Lookout, a cybersecurity firm. The apps contained three surveillance-focused malware: ViperRAT, Desert Scorpion, and FrozenCell. Although the apps were immediately taken down after the report, thousands of users had already downloaded the apps and became vulnerable to attacks.
Another set of fake banking apps were found on Google Play Store by antivirus company ESET last September. The apps impersonated six major banks from New Zealand, Australia, UK, Switzerland, and Poland. The fake banking apps relied on bogus forms to gather login details and valuable data related to the financial institutions being impersonated.
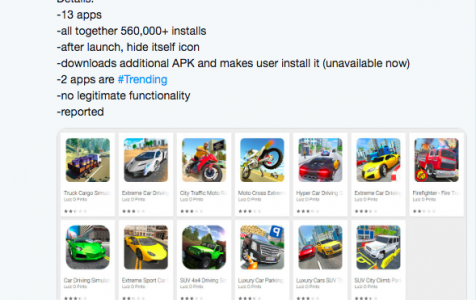
Just last week, the newest of these batches of malware apps on Google Play included 13 mobile apps published under the developer name Luiz O Pinto. These apps posed as driving or racing apps, and were downloaded by more than half a million users on Google Play Store.
New Threat
The 13 malicious apps in Google Play were discovered by Lukas Stefanko, an Android security researcher. He warned about the apps in a series of Twitter posts, such as the one below:
According to Stefanko, the games were just a cover to allow access to the malware in the background. He even said that two of the 13 fake apps – namely Car Driving Simulator and Luxury Cars SUV – are on the trending list on Google Play Store, placing third and ninth in the Top New Free Racing Games when they were still available for download.
The apps have been removed from Google Play Store , but Softonic was able to list down some of these malicious apps by Luiz O Pinto, including Extreme Car Driving City, Hyper Car Driving Simulator, Moto Cross Extreme Racing, Luxury Cars SUV Traffic, Firefighter Fire Truck Simulator, Extreme Car Driving Racing, Truck Cargo Simulator, Extreme Sport Car Driving, and SUV 4×4 Driving Simulator. The apps had zero downloads.
How Do These Malicious Apps Work?
When a user downloads the app, the installation process looks the same as with other normal apps. However, once the installation is completed, the app hides the game icon, making users think that the installation has failed. The apps themselves have no legitimate functionality and only serve as a cover for the malware download.
Once the game is installed, the user will be prompted to download an extra APK Android application package, which is, in fact, the malware. The malware disguises as a Game Center app and needs the permission of the user to be installed. But because most users think that the previous installation failed, it become s easier for them to be convinced to download the second app, thinking that it might be a necessary component for the driving app to work.
What they don’t know is that they’re actually installing the malware itself. This malware displays ads once the device is unlocked , and this surge of activity causes the Android device to slow down noticeably.
Stefanko was unable to determine what malware family was behind these fake apps, but anti-malware scans labeled it as a Trojan. The fake car simulators and racing games were taken down from Google Play after Stefanko reported his discovery. However, the apps had already been downloaded by 560,000 users by then.
What to Do
If you think you’re one of those who downloaded one of these fake apps, the first thing you need to is to uninstall the app. But since the game icon is hidden, you need to go to Settings > Apps or Applications and find the suspicious app from the list. Tap the app you want to remove, then tap Uninstall.
Note that uninstalling the app does not mean that your device is no longer infected. To totally remove the threat, you need to run an antivirus software that can detect the malware. Anti-malware scans, for instance, labeled the malware as a Hiddad Android Trojan, which is known for prompting users to give 5-star ratings to the apps it supports in order to boost store ratings.
Once the malware has been deleted, you should also delete all junk files on your phone to avoid leaving behind any traces of the malware.
How To Detect Fake or Malicious Apps
Malicious apps are hard to detect, and more often than not, you only realize your mistake once you’ve installed them. But when you know the telltale signs of a fake app, it will be easier to avoid downloading them and compromising your device in the first place.
Here are some tips to make sure you’re downloading the correct app and not a fake one. Note that even though malicious apps can sneak their way into Google Play Store, it is still the safest place to download Android apps from.
- Check the reviews and ratings. Most malware apps on Google Play have bad reviews and poor ratings. The 13 malicious apps in Google Play mentioned in this article, for example, had very bad reviews warning other users not to download the apps because they were malicious.
- Check the description, if the app has one. Some fake apps don’t bother to put any description at all. And if they do, they are most probably copied from elsewhere or spun from the original description.
- Watch out for the permission being requested during installation. In the case of these racing apps, one of the permissions allowed the apps to run during startup, which is already suspicious when you think about it. They were also asking for full network access, to view network connections and Wi-Fi connections. If you notice any red flags during installation, cancel the process immediately.
- If the app is not available on Google Play Store, search for the app on Google and look for the developer’s official website.
Once you encounter any of these red flags, stop the installation immediately and delete any downloaded files associated with the suspicious app.
Conclusion
Google has been trying to make it hard for malicious developers to upload fraudulent apps on the Play Store, but so far its efforts are yet to bear fruit. Google announced in June that it will be adding a string of security metadata to every Android APK to make sure the apps are authentic and verified. This new series of attacks only clearly shows that Google has to work a lot harder in order to keep these fake apps off Google Play.